一般在uboot里除了可以使用默认的env变量,还可以使用存自定义的env并且存储在外部存储介质(如flash)中,然后使能从存储介质读取加载env,当uboot加载env时候会检测env driver,若能成功读取存储介质的env分区并且crc校验成功后就会将env加载到uboot中。但是使用linux的mkenvimage生成的env镜像依旧是以明文形式存在flash中,若自定义了一些对于系统非常重要的env变量(如开机密码、一些key或者重要信息等),很容易从env窃取到重要的启动信息或其他内容。
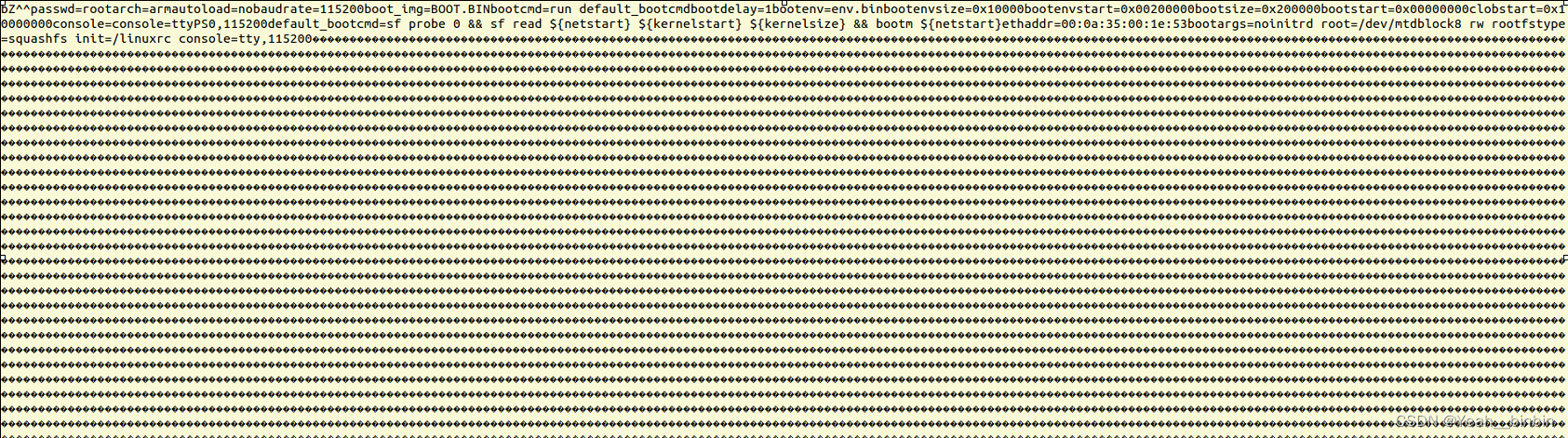
下图是使用mkenvimage生成并写入flash的env镜像。cat进入查看内容仍可以看到全部的明文信息,保密性不强。
因此这里实现一种对mkenvimage生成的env镜像加密并且在uboot读取env镜像后先进行解密再进行校验加载。综合考虑后使用AES对称加密,AES加密安全性高且uboot有相关的AES的接口。
简要提一下uboot里env的初始化大概流程:
board_init_r→init_sequence_r→initr_env→env_relocate→env_load(若没有使能了外部存储加载env则使用env_default.h默认的env)→找到对应存储介质的env driver→调用env driver→load→调用spi_flash_read根据ENV_SIZE和ENV_OFFSET读取flash的env镜像到内存buf->最后env_import将buf进行crc检验,检验成功后拷贝到uboot的env映射表中。
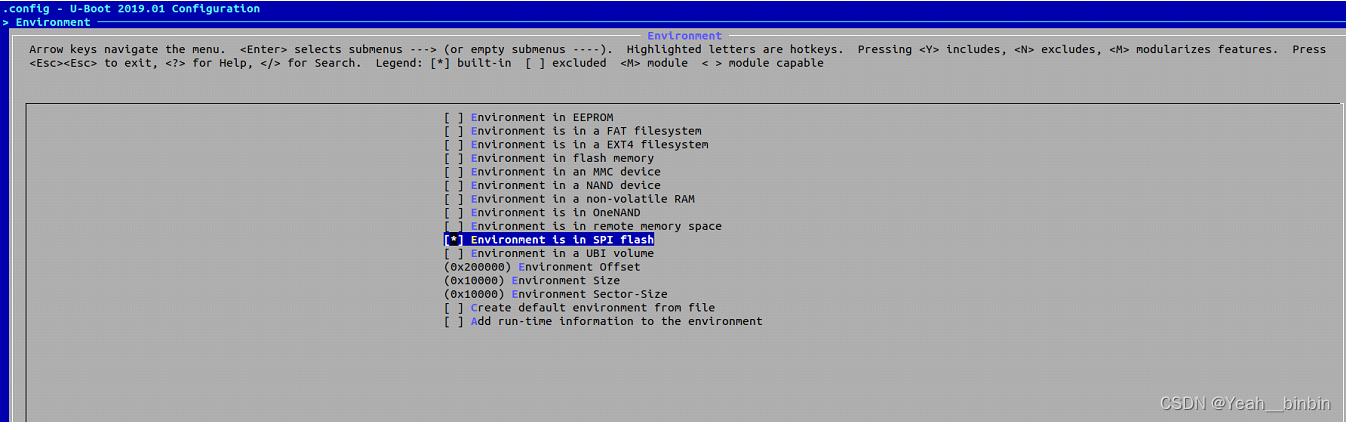
下图使能了从spi flash加载env
在PC上编写AES加密程序:
int main(int argc,char**argv)
{
u8 commkey[] = {
//128bits key,自行定义
0x12, 0x34, 0x56, 0x78,
0x27, 0x7E, 0x1B, 0xFD,
0xEE, 0x0A, 0x45, 0x50,
0x41, 0X83, 0X22, 0xF1};
if(argc!=3)
{
printf("[./env_encrypt] [src_file] [dst_file]\n");
return -1;
}
u32 size=0;
int i;
if (access(argv[1], F_OK)!=0) //加密的源文件
{
printf("%s not found!\n",argv[1]);
return -1;
}
FILE *fp_src=fopen(argv[1],"r+");
FILE *fp_dst=fopen(argv[2],"w+");
if(fp_src==NULL||fp_dst==NULL)
{
printf("fp =NULL\n");
return -1;
}
struct stat file_info;
stat(argv[1] ,&file_info);
size=file_info.st_size; //获得源文件大小
printf("src_file size=%d\n",size);
char buf[size];
char encrypt_data[size];
char decrypt_data[size];
memset(buf,0,size);
memset(encrypt_data,0,size);
int pos=0;
fread(buf,1,size,fp_src);
fclose(fp_src);
u8 tin[16];
u8 tout[16];
u8 expand_key[256];
memset(expand_key,0x00,256*sizeof(u8));
aes_expand_key(commkey, expand_key);//初始化和拓展aes key
for(i=0;i<size;i=i+16)
{
memset(tin,0x00,16);
memset(tout,0x00,16);
memcpy(tin,(char *)buf+i,16);
aes_encrypt(tin,expand_key,tout); //分组加密
memcpy(encrypt_data+i,tout,16);
}
fwrite(encrypt_data,1,size,fp_dst);
printf("encrypt ok\n");
fclose(fp_dst);
return 0;
}
在uboot->env->sf.c->env_sf_load(使用的是qspi flash,若不同的flash找到对应的驱动文件)添加AES解密步骤:
static int env_sf_load(void)
{
int ret;
char *buf = NULL;
buf = (char *)memalign(ARCH_DMA_MINALIGN, CONFIG_ENV_SIZE);
if (!buf) {
set_default_env("malloc() failed", 0);
return -EIO;
}
ret = setup_flash_device();
if (ret)
goto out;
ret = spi_flash_read(env_flash,
CONFIG_ENV_OFFSET, CONFIG_ENV_SIZE, buf); //从spi flash的偏移读取env镜像,在上图设置了CONFIG_ENV_OFFSET=0x200000 CONFIG_ENV_SIZE=0x10000
if (ret) {
set_default_env("spi_flash_read() failed", 0);
goto err_read;
}
#if defined MY_ENVENCRYPT
puts("decrypting env\n");
int i;
u8 tin[16];
u8 tout[16];
u8 commkey[] = {
//128bits key,自行定义,跟加密的key一样
0x12, 0x34, 0x56, 0x78,
0x27, 0x7E, 0x1B, 0xFD,
0xEE, 0x0A, 0x45, 0x50,
0x41, 0X83, 0X22, 0xF1};
u8 *expand_key = NULL;
expand_key = (u8 *)malloc(sizeof(u8)*256);
memset(expand_key,0x00,sizeof(u8)*256);
aes_expand_key(commkey, expand_key);
for(i=0;i<CONFIG_ENV_SIZE;i=i+16){
memset(tin,0x00,16);
memset(tout,0x00,16);
memcpy(tin,(char *)buf+i,16);
aes_decrypt(tin, expand_key, tout);//分组解密
memcpy(buf+i,tout,16);
}
free(expand_key);
printf("decrypting env ok \n");
#endif
ret = env_import(buf, 1);//该接口将解密得到的buf传入env映射表
if (!ret)
gd->env_valid = ENV_VALID;//设置全局变量gd的标志表示env加载成功
err_read:
spi_flash_free(env_flash);
env_flash = NULL;
out:
free(buf);
return ret;
}
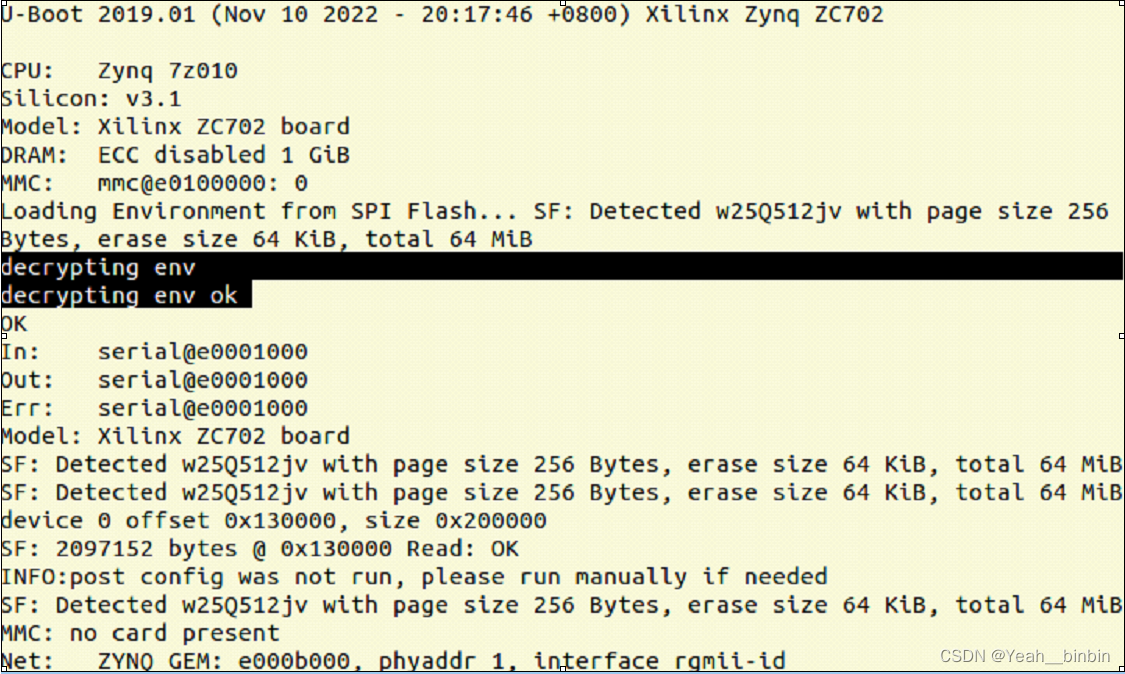
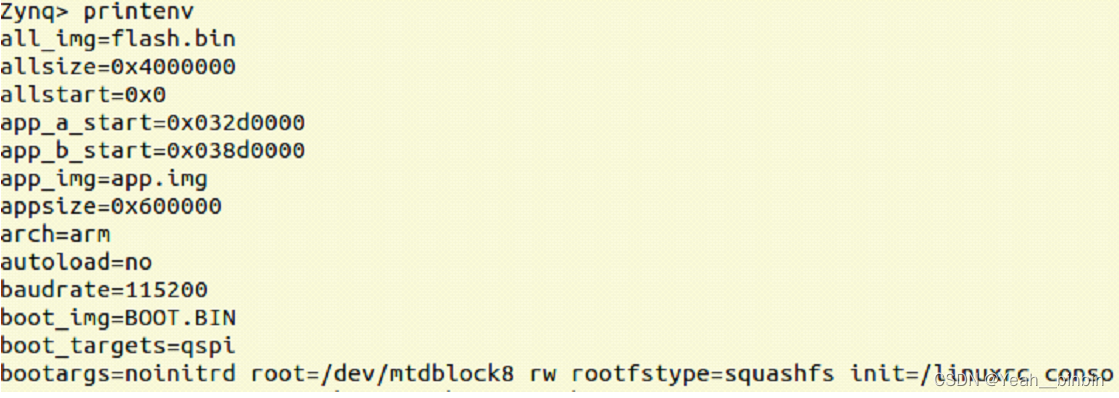
最后重新编译uboot,烧录uboot和加密后的env镜像到flash后重新启动uboot能正常加密和加载env,通过uboot命令行能查看到自定义变量。
举一反三,也可以用这种思路去加密kernel和rootfs,如果想进一步提高安全性,可以将秘钥写入CPU的硬件逻辑区域(前提是CPU支持,这里使用的xilinx zynq-7010是支持写入AES秘钥到可信硬件区域的EFUSE寄存器上(熔丝,只能写一次),然后加密二进制系统镜像并且在启动的时候使能硬解密引擎,解密后将镜像加载到内存实现安全启动的)。
附在uboot/lib/aes.c下有aes加解密源码
// SPDX-License-Identifier: GPL-2.0+
/*
* Copyright (c) 2011 The Chromium OS Authors.
* (C) Copyright 2011 NVIDIA Corporation www.nvidia.com
*/
/*
* advanced encryption standard
* author: karl malbrain, malbrain@yahoo.com
*
* This work, including the source code, documentation
* and related data, is placed into the public domain.
*
* The orginal author is Karl Malbrain.
*
* THIS SOFTWARE IS PROVIDED AS-IS WITHOUT WARRANTY
* OF ANY KIND, NOT EVEN THE IMPLIED WARRANTY OF
* MERCHANTABILITY. THE AUTHOR OF THIS SOFTWARE,
* ASSUMES _NO_ RESPONSIBILITY FOR ANY CONSEQUENCE
* RESULTING FROM THE USE, MODIFICATION, OR
* REDISTRIBUTION OF THIS SOFTWARE.
*/
#ifndef USE_HOSTCC
#include <common.h>
#else
#include <string.h>
#endif
#include "uboot_aes.h"
/* forward s-box */
static const u8 sbox[256] = {
0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5,
0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76,
0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0,
0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0,
0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc,
0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15,
0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a,
0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75,
0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0,
0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84,
0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b,
0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf,
0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85,
0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8,
0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5,
0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2,
0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17,
0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73,
0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88,
0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb,
0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c,
0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79,
0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9,
0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08,
0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6,
0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a,
0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e,
0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e,
0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94,
0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf,
0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68,
0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16
};
/* inverse s-box */
static const u8 inv_sbox[256] = {
0x52, 0x09, 0x6a, 0xd5, 0x30, 0x36, 0xa5, 0x38,
0xbf, 0x40, 0xa3, 0x9e, 0x81, 0xf3, 0xd7, 0xfb,
0x7c, 0xe3, 0x39, 0x82, 0x9b, 0x2f, 0xff, 0x87,
0x34, 0x8e, 0x43, 0x44, 0xc4, 0xde, 0xe9, 0xcb,
0x54, 0x7b, 0x94, 0x32, 0xa6, 0xc2, 0x23, 0x3d,
0xee, 0x4c, 0x95, 0x0b, 0x42, 0xfa, 0xc3, 0x4e,
0x08, 0x2e, 0xa1, 0x66, 0x28, 0xd9, 0x24, 0xb2,
0x76, 0x5b




 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 1008
1008

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










