参考文章:Centos7主机升级OpenSSH9.3版本_centos7升级openssh9.3-优快云博客
1.关闭防火墙、备份/etc/ssh、/etc/pam.d
systemctl stop firewalld
cp -r -a /etc/ssh/ /xx/ssh.bak/
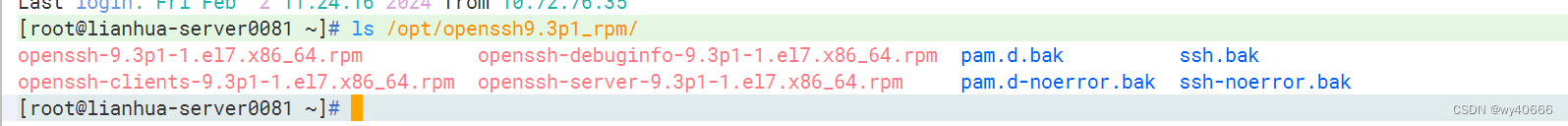
cp -r -a /etc/pam.d/ /xx/pam.d.bak/2.上传rpm包,网上有资源 动点脑子可以省点米
3.通过自行编译RPM安装包,可以在不同主机上快速部署新版OpenSSH的新版本
#执行更新操作
rpm -Uvh openssh-*.rpm4.还原备份文件
cp -r /xx/pam.d.bak/sshd /etc/pam.d/sshd
cp -r /xx/ssh.bak/sshd_config /etc/ssh/sshd_config5.关于/etc/pam.d/sshd 、/etc/ssh/sshd_config的内容:我先在别的机器的成功过,但后面有的机器还原了备份也有问题,我对比成功机器和问题机器/etc/pam.d/sshd 、/etc/ssh/sshd_config的内容,发现差别挺大。后面我这两文件的内容全用成功机器里的(拷过来pam.d-noerror.bak 、ssh-noerror.bak或者直接复制粘贴)代替了,后面也通了。附上内容
#cat /opt/openssh9.3p1_rpm/pam.d-noerror.bak/sshd
#%PAM-1.0
auth required pam_sepermit.so
auth substack password-auth
auth include postlogin
## Used with polkit to reauthorize users in remote sessions
#-auth optional pam_reauthorize.so prepare
account required pam_nologin.so
account include password-auth
password include password-auth
## pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
## pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session required pam_namespace.so
session optional pam_keyinit.so force revoke
session include password-auth
session include postlogin
## Used with polkit to reauthorize users in remote sessions
-session optional pam_reauthorize.so prepare#cat /opt/openssh9.3p1_rpm/ssh-noerror.bak/sshd_config
# $OpenBSD: sshd_config,v 1.100 2016/08/15 12:32:04 naddy Exp $
# This is the sshd server system-wide configuration file. See
# sshd_config(5) for more information.
# This sshd was compiled with PATH=/usr/local/bin:/usr/bin
# The strategy used for options in the default sshd_config shipped with
# OpenSSH is to specify options with their default value where
# possible, but leave them commented. Uncommented options override the
# default value.
# If you want to change the port on a SELinux system, you have to tell
# SELinux about this change.
# semanage port -a -t ssh_port_t -p tcp #PORTNUMBER
#
#Port 22
#AddressFamily any
#ListenAddress 0.0.0.0
#ListenAddress ::
HostKey /etc/ssh/ssh_host_rsa_key
#HostKey /etc/ssh/ssh_host_dsa_key
HostKey /etc/ssh/ssh_host_ecdsa_key
HostKey /etc/ssh/ssh_host_ed25519_key
# Ciphers and keying
#RekeyLimit default none
# Logging
#SyslogFacility AUTH
SyslogFacility AUTHPRIV
#LogLevel INFO
# Authentication:
#LoginGraceTime 2m
#PermitRootLogin yes
#StrictModes yes
#MaxAuthTries 6
#MaxSessions 10
#PubkeyAuthentication yes
# The default is to check both .ssh/authorized_keys and .ssh/authorized_keys2
# but this is overridden so installations will only check .ssh/authorized_keys
AuthorizedKeysFile .ssh/authorized_keys
#AuthorizedPrincipalsFile none
#AuthorizedKeysCommand none
#AuthorizedKeysCommandUser nobody
# For this to work you will also need host keys in /etc/ssh/ssh_known_hosts
#HostbasedAuthentication no
# Change to yes if you don't trust ~/.ssh/known_hosts for
# HostbasedAuthentication
#IgnoreUserKnownHosts no
# Don't read the user's ~/.rhosts and ~/.shosts files
#IgnoreRhosts yes
# To disable tunneled clear text passwords, change to no here!
#PasswordAuthentication yes
#PermitEmptyPasswords no
PasswordAuthentication yes
# Change to no to disable s/key passwords
#ChallengeResponseAuthentication yes
ChallengeResponseAuthentication no
# Kerberos options
#KerberosAuthentication no
#KerberosOrLocalPasswd yes
#KerberosTicketCleanup yes
#KerberosGetAFSToken no
#KerberosUseKuserok yes
# GSSAPI options
GSSAPIAuthentication yes
GSSAPICleanupCredentials no
#GSSAPIStrictAcceptorCheck yes
#GSSAPIKeyExchange no
#GSSAPIEnablek5users no
# Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# be allowed through the ChallengeResponseAuthentication and
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication via ChallengeResponseAuthentication may bypass
# the setting of "PermitRootLogin without-password".
# If you just want the PAM account and session checks to run without
# PAM authentication, then enable this but set PasswordAuthentication
# and ChallengeResponseAuthentication to 'no'.
# WARNING: 'UsePAM no' is not supported in Red Hat Enterprise Linux and may cause several
# problems.
UsePAM yes
#AllowAgentForwarding yes
#AllowTcpForwarding yes
#GatewayPorts no
X11Forwarding yes
#X11DisplayOffset 10
#X11UseLocalhost yes
#PermitTTY yes
#PrintMotd yes
#PrintLastLog yes
#TCPKeepAlive yes
#UseLogin no
#UsePrivilegeSeparation sandbox
#PermitUserEnvironment no
#Compression delayed
#ClientAliveInterval 0
#ClientAliveCountMax 3
#ShowPatchLevel no
#UseDNS yes
#PidFile /var/run/sshd.pid
#MaxStartups 10:30:100
#PermitTunnel no
#ChrootDirectory none
#VersionAddendum none
# no default banner path
#Banner none
# Accept locale-related environment variables
AcceptEnv LANG LC_CTYPE LC_NUMERIC LC_TIME LC_COLLATE LC_MONETARY LC_MESSAGES
AcceptEnv LC_PAPER LC_NAME LC_ADDRESS LC_TELEPHONE LC_MEASUREMENT
AcceptEnv LC_IDENTIFICATION LC_ALL LANGUAGE
AcceptEnv XMODIFIERS
# override default of no subsystems
Subsystem sftp /usr/libexec/openssh/sftp-server
# Example of overriding settings on a per-user basis
#Match User anoncvs
# X11Forwarding no
# AllowTcpForwarding no
# PermitTTY no
# ForceCommand cvs server
PermitRootLogin yes
HostKeyAlgorithms ssh-rsa,ssh-dsssshd_config最后两行“PermitRootLogin yes 、HostKeyAlgorithms ssh-rsa,ssh-dss”是后来添加的
ssh升级后,为了安全,默认不再采用原来一些加密算法。所以补充了这两行参数。
6.删除ssh密钥
rm -rf /etc/ssh/ssh_host_*
#如果发现dsa密钥缺了
ssh-keygen -t dsa -f /etc/ssh/ssh_host_dsa_key7.重启sshd服务
# 查看状态
systemctl status sshd
# 重启sshd
systemctl restart sshd
# 再查看sshd状态
systemctl status sshd
#查看版本
ssh -V至此差不多大功告成了。
8.再说说别的坑吧。升级完后,我的几台机器ssh连不上了,查明原因:公匙改变了。
解决办法:
修改 ~/.ssh下的文件内容,文件没有就新建。
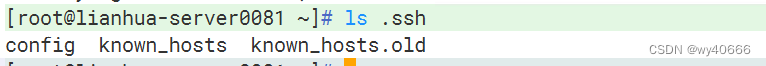
#新建config文件
touch config
#编辑config内容
vim config
Host *
HostkeyAlgorithms +ssh-rsa
PubkeyAcceptedKeyTypes +ssh-rsa然后再清空known_hosts文件中连不上的那几台机器的旧公匙内容。
最后也是解决了。
2024.2.22 升级到openssh9.6遇到问题
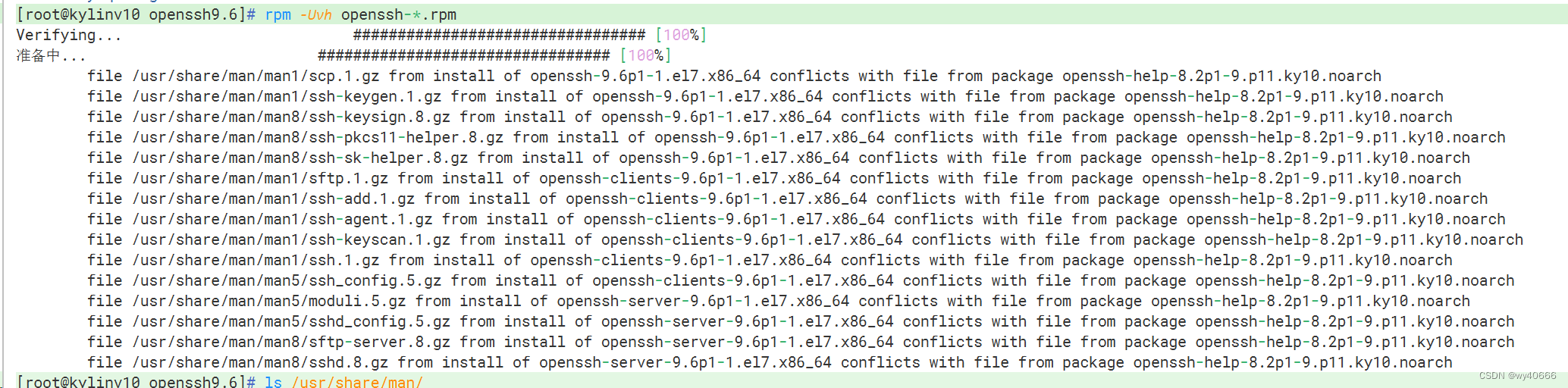
这段信息表明在尝试使用 rpm 命令更新或安装 openssh 包时遇到了冲突。具体来说,您试图安装或升级到 openssh-9.6p1 的某个版本,但系统中已经安装了与这个新版本有文件冲突的 openssh-help-8.2p1-9.p11.ky10.noarch 包。
解决办法:卸载原有的openssh
yum -y remove openssh-help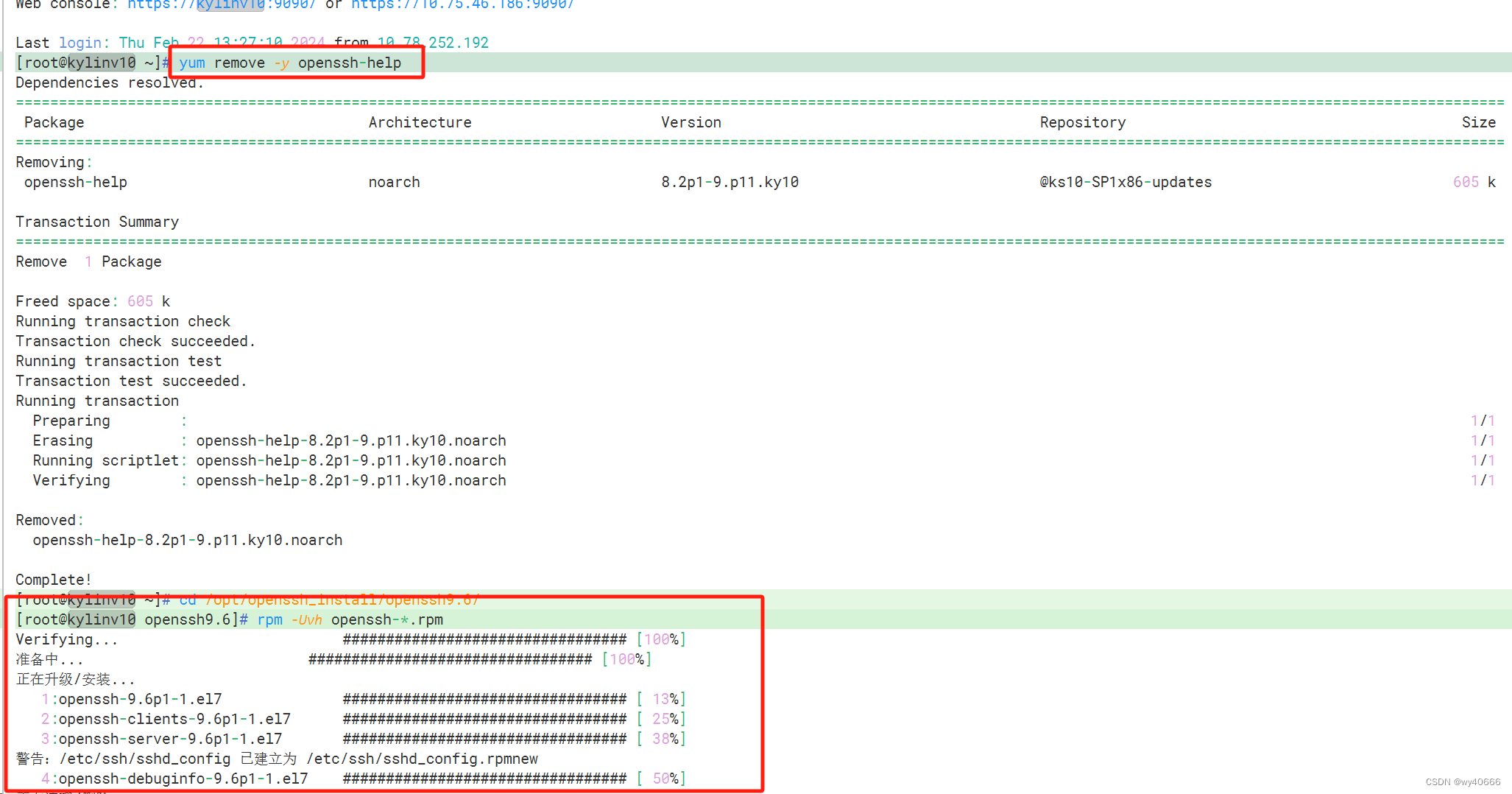







 本文详细描述了在CentOS7系统中升级OpenSSH从9.3到9.6版本的过程,包括关闭防火墙、备份配置文件、安装RPM包、解决公钥冲突等步骤,以及遇到的问题和解决方法。
本文详细描述了在CentOS7系统中升级OpenSSH从9.3到9.6版本的过程,包括关闭防火墙、备份配置文件、安装RPM包、解决公钥冲突等步骤,以及遇到的问题和解决方法。
















 497
497

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








