1. sm4 分组密码算法
2. 直接进代码
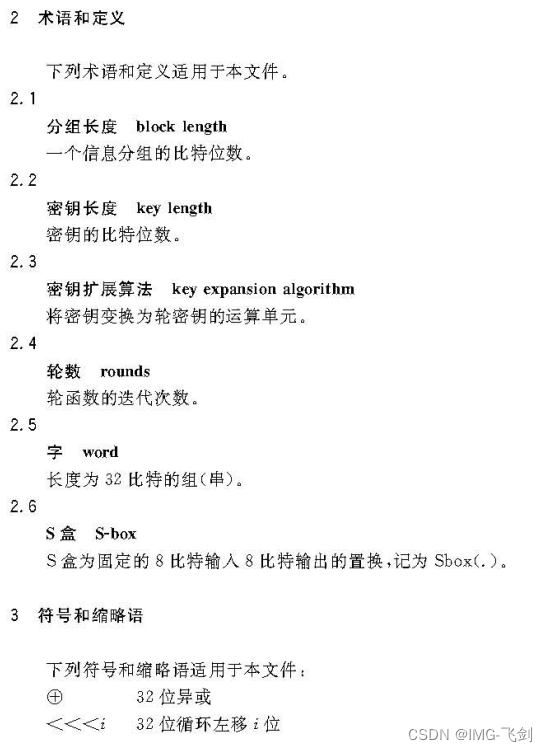
需要同步观看sm算法 国密标准下面有。
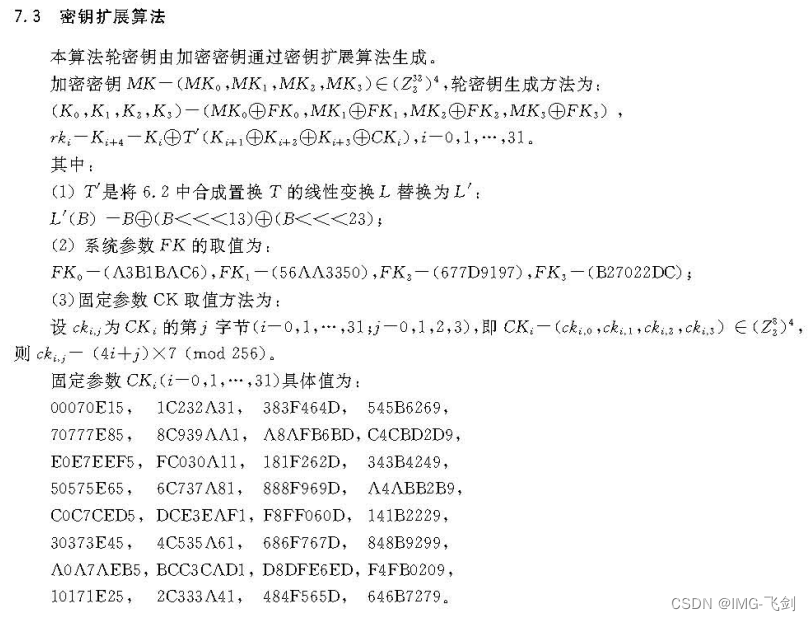
密钥设置,生成轮密钥
//密钥设置
static void sm4_setkey( unsigned long RK[32], unsigned char key[16] )
{
//加密密钥 MK = (MK0, MK1, MK2, MK3)
unsigned long MK[4];
unsigned long k[36];
unsigned long i = 0;
//设置传入密钥至MK
GET_ULONG_BE( MK[0], key, 0 );
GET_ULONG_BE( MK[1], key, 4 );
GET_ULONG_BE( MK[2], key, 8 );
GET_ULONG_BE( MK[3], key, 12 );
//密钥扩展算法
//1. 密钥MK(i)与系统参数FK(i)异或 (K0, K1, K2, K3) = (MK0 ^ FK0, MK1 ^ FK1, MK2 ^ FK2, MK3 ^ FK3)
k[0] = MK[0]^FK[0];
k[1] = MK[1]^FK[1];
k[2] = MK[2]^FK[2];
k[3] = MK[3]^FK[3];
//2. 通过K(i)和CK(i)(固定参数)计算得到轮密钥: 获取轮密钥 rk(i) = K(i+4) = K(i) ^ T' ( K(i+1) ^ K(i+2) ^ K(i+3) ^ CK(i) )
for(; i<32; i++)
{
//sm4CalciRK 生成 T'( K(i+1) ^ K(i+2) ^ K(i+3) ^ CK(i) )
k[i+4] = k[i] ^ (sm4CalciRK(k[i+1]^k[i+2]^k[i+3]^CK[i]));
RK[i] = k[i+4];
}
}
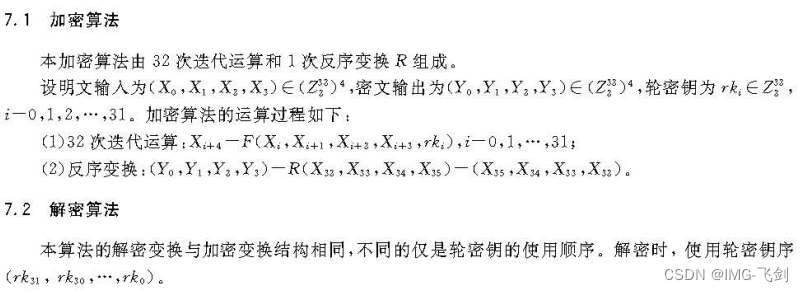
加解密算法描述
void sm4_enc_128bit(unsigned long rk[32], unsigned char input[16], unsigned char output[16])
{
sm4_one_round( rk, input, output);
}
void sm4_dec_128bit(unsigned long rk[32], unsigned char input[16], unsigned char output[16])
{
int i;
unsigned long rk_temp[32];
//sm4 解密是将轮密钥反序使用
for( i = 0; i < 32; i ++ )
{
rk_temp[i] = rk[31-i] ;
}
sm4_one_round( rk_temp, input, output);
}
32次迭代和反序变换再sm4_one_round 实际实现内部。
实际的算法实现
static unsigned char sm4Sbox(unsigned char inch)
{
unsigned char *pTable = (unsigned char *)SboxTable;
unsigned char retVal = (unsigned char)(pTable[inch]);
return retVal;
}
static unsigned long sm4Lt(unsigned long ka)
{
// T 是一个可逆变换, 由一个非线性变换和一个线性变换复合而成
unsigned long bb = 0;
unsigned long c = 0;
unsigned char a[4];
unsigned char b[4];
//将输入的A(a0, a1, a2, a3) 通过S盒变换输出 B(b0, b1, b2, b3) -- 非线性变换
//S盒取值--输入EF 则表示取S盒的第E行第F列数据 S(EF)= 84; S盒的数据是固定的 Sbox(a0)
PUT_ULONG_BE(ka,a,0)
b[0] = sm4Sbox(a[0]);
b[1] = sm4Sbox(a[1]);
b[2] = sm4Sbox(a[2]);
b[3] = sm4Sbox(a[3]);
//将数据以大端形式转换为ulong
GET_ULONG_BE(bb,b,0)
//一个线性变换L C = L(B) = B ^ (B<<<2) ^ (B<<<10) ^ (B<<<18) ^ (B<<<24);
c =bb^(ROTL(bb, 2))^(ROTL(bb, 10))^(ROTL(bb, 18))^(ROTL(bb, 24));
return c;
}
static unsigned long sm4F(unsigned long x0, unsigned long x1, unsigned long x2, unsigned long x3, unsigned long rk)
{
//执行轮函数 F(Xi, X(i+1), X(i+2), X(i+3), rk(i)) = Xi ^ T(X(i+1) ^ X(i+2) ^ X(i+3) ^ rk(i))
// T 是一个可逆变换, 由一个非线性变换和一个线性变换复合而成
return (x0^sm4Lt(x1^x2^x3^rk));
}
static void sm4_one_round( unsigned long sk[32], unsigned char input[16], unsigned char output[16] )
{
//一轮128位数据计算由 32次迭代运算和1次反序变换R组成
unsigned long i = 0;
//最终数据会多出4个字节数据,用于返回的输出值
unsigned long ulbuf[36];
//明文数据(X0, X1, X2, X3)设置ulbuf
memset(ulbuf, 0, sizeof(ulbuf));
GET_ULONG_BE( ulbuf[0], input, 0 )
GET_ULONG_BE( ulbuf[1], input, 4 )
GET_ULONG_BE( ulbuf[2], input, 8 )
GET_ULONG_BE( ulbuf[3], input, 12 )
//1. 32次的迭代运算 其中F 是轮函数 F(X0, X1, X2, X3, rk) = X0 ^ T(X1 ^ X2 ^ X3 ^ rk)
while(i<32)
{
//执行轮函数 F(Xi, X(i+1), X(i+2), X(i+3), rk(i)) = Xi ^ T(X(i+1) ^ X(i+2) ^ X(i+3) ^ rk(i))
ulbuf[i+4] = sm4F(ulbuf[i], ulbuf[i+1], ulbuf[i+2], ulbuf[i+3], sk[i]);
i++;
}
//输出数据,包含了反序变换 (Y0, Y1, Y2, Y3) = R(X32, X33, X34, X35) = (X35, X34, X33, X32)
PUT_ULONG_BE(ulbuf[35],output,0);
PUT_ULONG_BE(ulbuf[34],output,4);
PUT_ULONG_BE(ulbuf[33],output,8);
PUT_ULONG_BE(ulbuf[32],output,12);
}
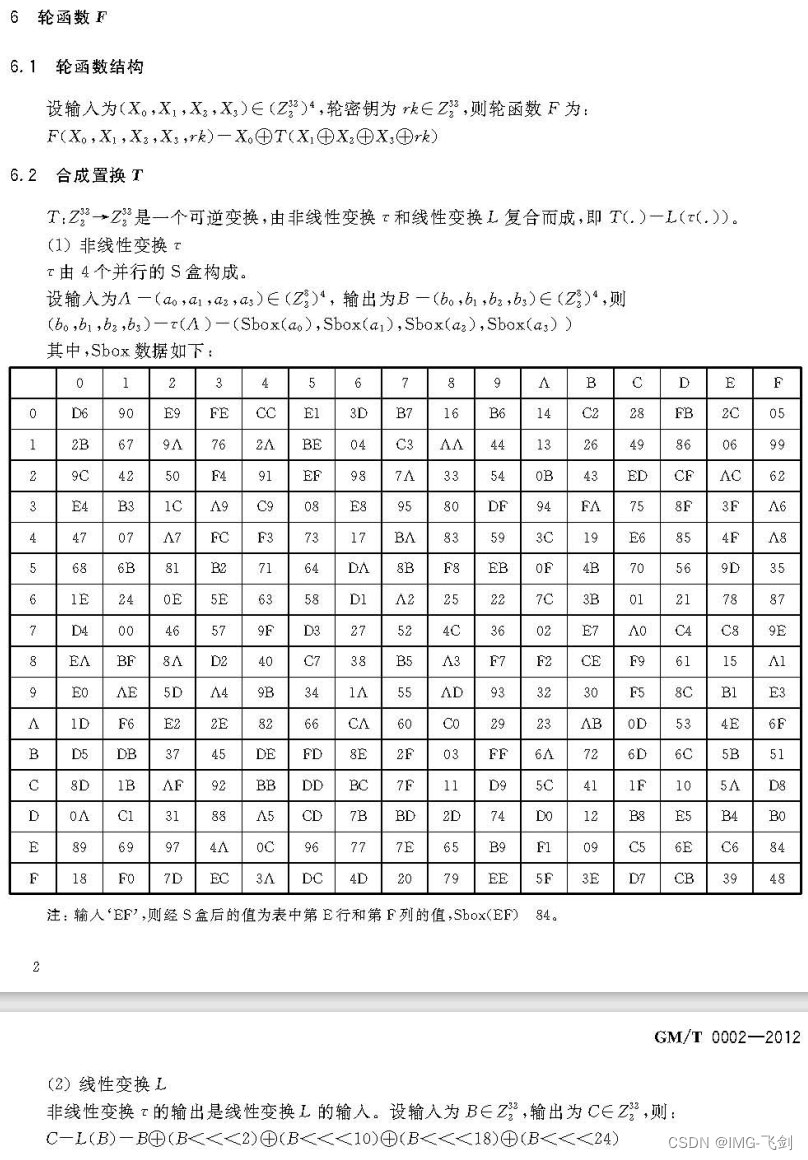
S盒 系统参数 固定参数
static const unsigned char SboxTable[16][16] =
{
{0xd6,0x90,0xe9,0xfe,0xcc,0xe1,0x3d,0xb7,0x16,0xb6,0x14,0xc2,0x28,0xfb,0x2c,0x05},
{0x2b,0x67,0x9a,0x76,0x2a,0xbe,0x04,0xc3,0xaa,0x44,0x13,0x26,0x49,0x86,0x06,0x99},
{0x9c,0x42,0x50,0xf4,0x91,0xef,0x98,0x7a,0x33,0x54,0x0b,0x43,0xed,0xcf,0xac,0x62},
{0xe4,0xb3,0x1c,0xa9,0xc9,0x08,0xe8,0x95,0x80,0xdf,0x94,0xfa,0x75,0x8f,0x3f,0xa6},
{0x47,0x07,0xa7,0xfc,0xf3,0x73,0x17,0xba,0x83,0x59,0x3c,0x19,0xe6,0x85,0x4f,0xa8},
{0x68,0x6b,0x81,0xb2,0x71,0x64,0xda,0x8b,0xf8,0xeb,0x0f,0x4b,0x70,0x56,0x9d,0x35},
{0x1e,0x24,0x0e,0x5e,0x63,0x58,0xd1,0xa2,0x25,0x22,0x7c,0x3b,0x01,0x21,0x78,0x87},
{0xd4,0x00,0x46,0x57,0x9f,0xd3,0x27,0x52,0x4c,0x36,0x02,0xe7,0xa0,0xc4,0xc8,0x9e},
{0xea,0xbf,0x8a,0xd2,0x40,0xc7,0x38,0xb5,0xa3,0xf7,0xf2,0xce,0xf9,0x61,0x15,0xa1},
{0xe0,0xae,0x5d,0xa4,0x9b,0x34,0x1a,0x55,0xad,0x93,0x32,0x30,0xf5,0x8c,0xb1,0xe3},
{0x1d,0xf6,0xe2,0x2e,0x82,0x66,0xca,0x60,0xc0,0x29,0x23,0xab,0x0d,0x53,0x4e,0x6f},
{0xd5,0xdb,0x37,0x45,0xde,0xfd,0x8e,0x2f,0x03,0xff,0x6a,0x72,0x6d,0x6c,0x5b,0x51},
{0x8d,0x1b,0xaf,0x92,0xbb,0xdd,0xbc,0x7f,0x11,0xd9,0x5c,0x41,0x1f,0x10,0x5a,0xd8},
{0x0a,0xc1,0x31,0x88,0xa5,0xcd,0x7b,0xbd,0x2d,0x74,0xd0,0x12,0xb8,0xe5,0xb4,0xb0},
{0x89,0x69,0x97,0x4a,0x0c,0x96,0x77,0x7e,0x65,0xb9,0xf1,0x09,0xc5,0x6e,0xc6,0x84},
{0x18,0xf0,0x7d,0xec,0x3a,0xdc,0x4d,0x20,0x79,0xee,0x5f,0x3e,0xd7,0xcb,0x39,0x48}
};
/* System parameter */
static const unsigned long FK[4] = {0xa3b1bac6,0x56aa3350,0x677d9197,0xb27022dc};
/* fixed parameter */
static const unsigned long CK[32] =
{
0x00070e15,0x1c232a31,0x383f464d,0x545b6269,
0x70777e85,0x8c939aa1,0xa8afb6bd,0xc4cbd2d9,
0xe0e7eef5,0xfc030a11,0x181f262d,0x343b4249,
0x50575e65,0x6c737a81,0x888f969d,0xa4abb2b9,
0xc0c7ced5,0xdce3eaf1,0xf8ff060d,0x141b2229,
0x30373e45,0x4c535a61,0x686f767d,0x848b9299,
0xa0a7aeb5,0xbcc3cad1,0xd8dfe6ed,0xf4fb0209,
0x10171e25,0x2c333a41,0x484f565d,0x646b7279
};
代码参考:
/*
- SM4 Encryption alogrithm (SMS4 algorithm)
- GM/T 0002-2012 Chinese National Standard ref:http://www.oscca.gov.cn/
- thanks to Xyssl
- thnaks and refers to http://hi.baidu.com/numax/blog/item/80addfefddfb93e4cf1b3e61.html
- author:goldboar
- email:goldboar@163.com
- 2012-4-20
*/

























 928
928

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










