由于电脑安装的了两个不同版本的.Net,导致之前所有的基于VS2012的Console程序都无法调试。但编译的exe可以正常运行。
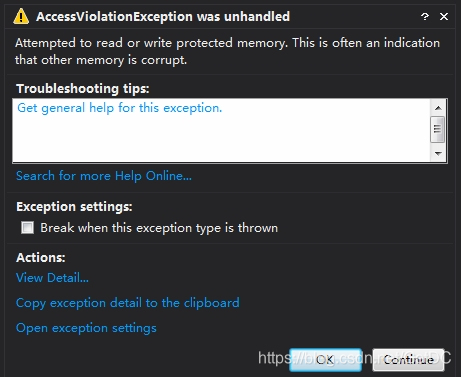
调试过程提示如下错误:
Attempted to read or write protected memory. This is often an indication that other memory is corrupt.
这个错误是尝试读取或写入受保护的内存。这通常表明其他内存已损坏。我猜测是由于读取Win32的DLL但没有释放导致的错误。如下图:
尝试以下各种方案均无效
- 更换更高版本的Framework版本。
- 运行netsh winsock reset
- 删除所有引用
- 修改为X86的编译版本
最后通过如下配置解决了问题:
Debug 标签 -> 在Enable Debuggers中 -> 选择Enable native code debugging
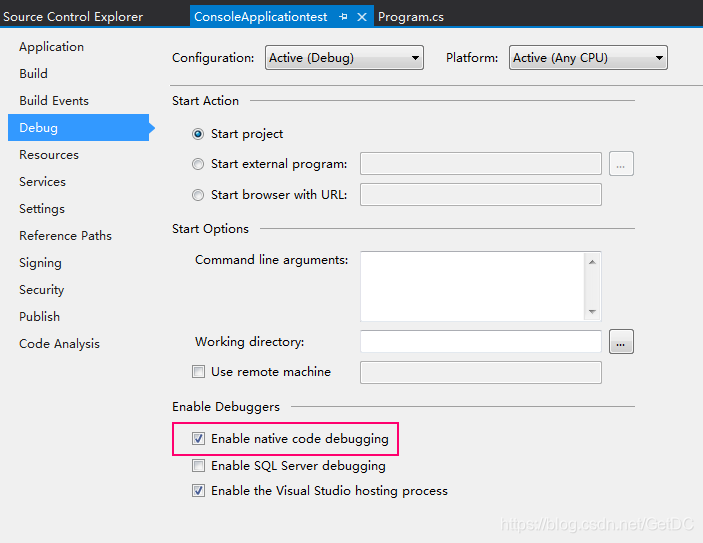
保存项目,F5调试,恢复正常。
总结一下:
这个问题似乎与.NET 4.5.1有关,4.5与更高版本的Frameword有兼容问题。后续搜索,可能下载并安装.NET 4.5.2也能解决问题。但还没有尝试过。







 本文解决了一个因电脑安装了两个不同版本的.NET而导致基于VS2012的Console程序无法调试的问题。通过启用本机代码调试功能,成功修复了Attempted to read or write protected memory的错误。
本文解决了一个因电脑安装了两个不同版本的.NET而导致基于VS2012的Console程序无法调试的问题。通过启用本机代码调试功能,成功修复了Attempted to read or write protected memory的错误。
















 1312
1312

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








