PL/SQL Engine
PL/SQL Engine
The PL/SQL compilation and runtime system is an engine that compiles and runs PL/SQL units.
The engine can be installed in the database or in an application development tool, such as Oracle Forms.
In either environment, the PL/SQL engine accepts as input any valid PL/SQL unit. The engine runs procedural statements, but sends SQL statements to the SQL engine in the database
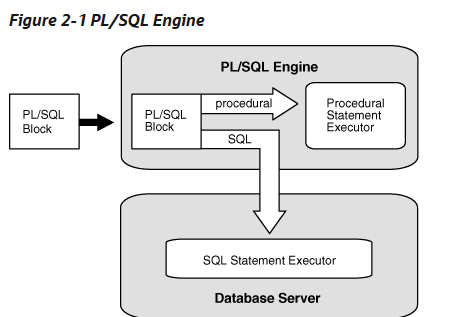
Typically, the database processes PL/SQL units.
When an application development tool processes PL/SQL units, it passes them to its local PL/SQL engine. If a PL/SQL unit contains no SQL statements, the local engine processes the entire PL/SQL unit. This is useful if the application development tool can benefit from conditional and iterative control.
For example, Oracle Forms applications frequently use SQL statements to test the values of field entries and do simple computations. By using PL/SQL instead of SQL, these applications can avoid calls to the database.
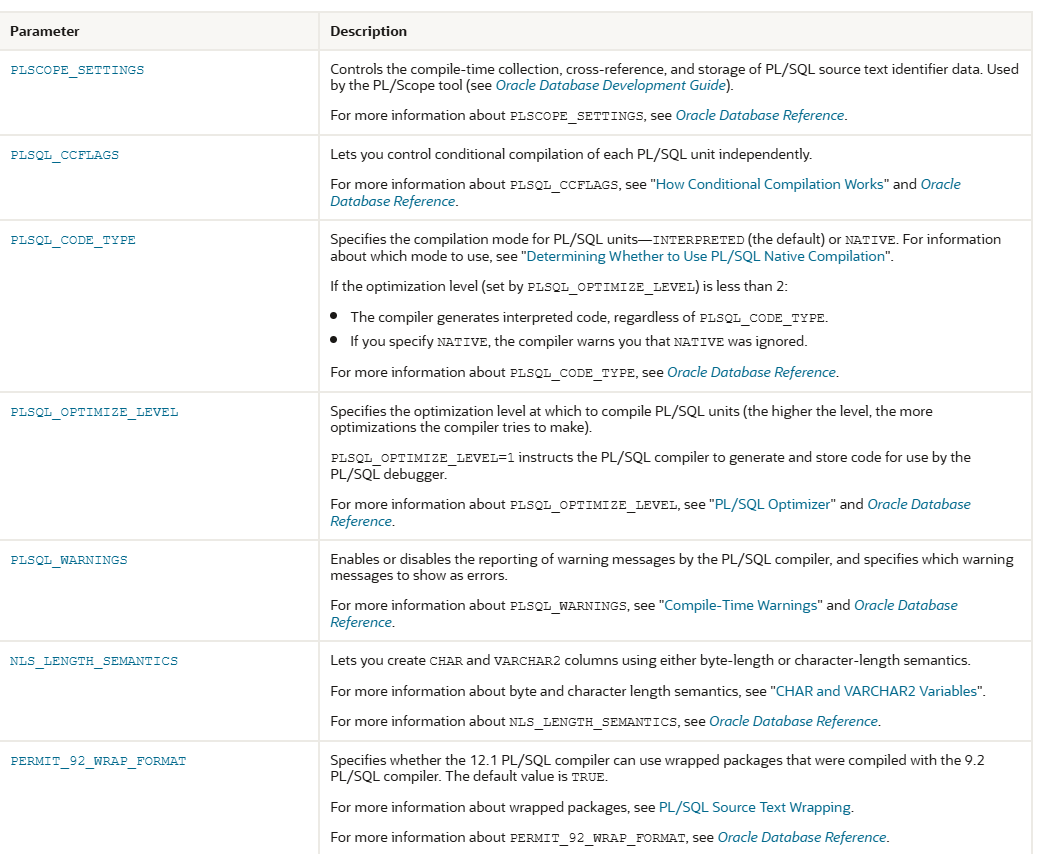
PL/SQL Units and Compilation Parameters
PL/SQL units are affected by PL/SQL compilation parameters (a category of database initialization parameters). Different PL/SQL units—for example, a package specification and its body—can have different compilation parameter settings.
A PL/SQL unit is one of these:
PL/SQL anonymous block
FUNCTION
LIBRARY
PACKAGE
PACKAGE BODY
PROCEDURE
TRIGGER
TYPE
TYPE BODY
Table 2-2 PL/SQL Compilation Parameters
Protecting Sensitive Information in PL/SQL
Data security should be a top priority during any application development. There are several ways you can mitigate the risk of vulnerabilities while using PL/SQL.
Be aware that the content of a PL/SQL block may be written in its entirety in such places as audit logs and trace files. Similarly, stored procedure code can be accessed through dictionary views, such as USER_SOURCE. For this reason, it is strongly recommended that you never include any sensitive information in a literal seen in PL/SQL code.
Bind variables can be used to help protect against SQL injection attacks, however, bind values can be visible in places such as trace files, audit, and V$SQL and related views. Access should be strictly managed to ensure that only those who require it have privileges to view this particularly sensitive information.
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








