JADX 上场
为了知道他做了什么,我们需要逆向出目前受害者的代码。这里我们使用开源项目jadx来完成。
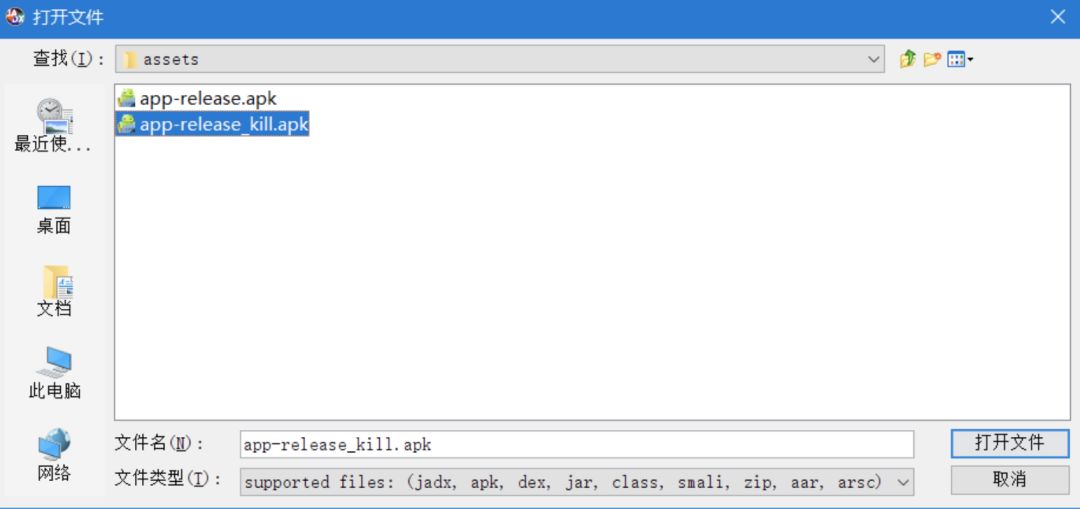
打开 jadx 之后会直接弹出「打开」对话框,选取被破解的 apk 即可:
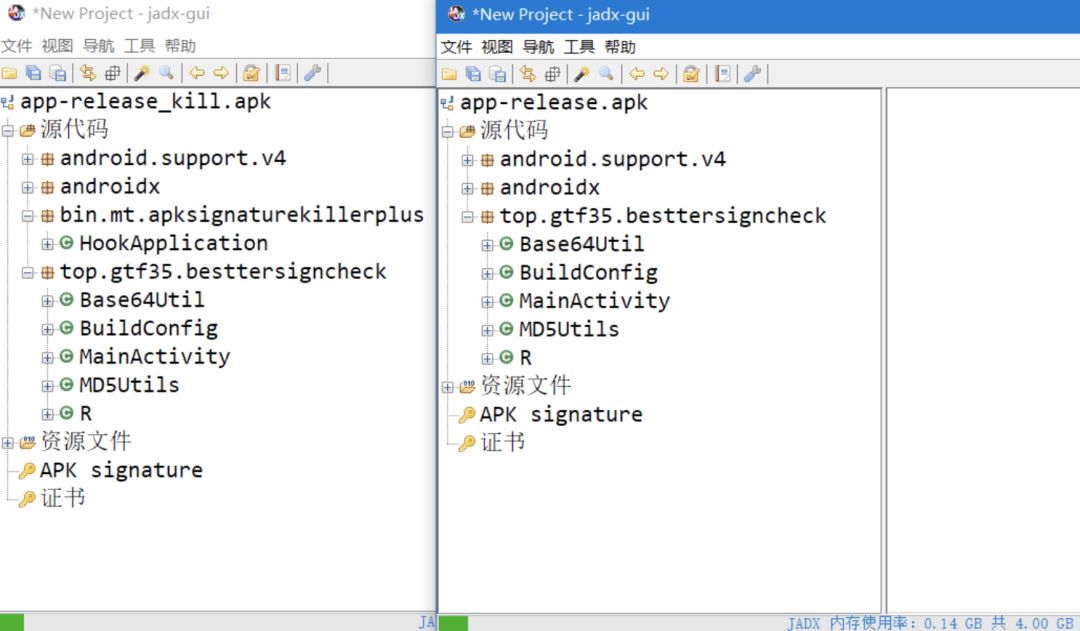
简单对比下可以发现,多了一个「HookApplication」类
点击进去即可直接看见源代码:
public class HookApplication extends Application implements InvocationHandler {
private static final int GET_SIGNATURES = 64;
private String appPkgName = BuildConfig.FLAVOR;
private Object base;
private byte[][] sign;
private void hook(Context context) {
try {
DataInputStream dataInputStream = new DataInputStream(new ByteArrayInputStream(Base64.decode(“省略很长的签名 base64”, 0)));
byte[][] bArr = new byte[(dataInputStream.read() & 255)][];
for (int i = 0; i < bArr.length; i++) {
bArr[i] = new byte[dataInputStream.readInt()];
dataInputStream.readFully(bArr[i]);
}
Class cls = Class.forName(“android.app.ActivityThread”);
Object invoke = cls.getDeclaredMethod(“currentActivityThread”, new Class[0
《Android学习笔记总结+最新移动架构视频+大厂安卓面试真题+项目实战源码讲义》
【docs.qq.com/doc/DSkNLaERkbnFoS0ZF】 完整内容开源分享
]).invoke(null, new Object[0]);
Field declaredField = cls.getDeclaredField(“sPackageManager”);
declaredField.setAccessible(true);
Object obj = declaredField.get(invoke);
Class cls2 = Class.forName(“android.content.pm.IPackageManager”);
this.base = obj;
this.sign = bArr;
this.appPkgName = context.getPackageName();
Object newProxyInstance = Proxy.newProxyInstance(cls2.getClassLoader(), new Class[]{cls2}, this);
declaredField.set(invoke, newProxyInstance);
PackageManager packageManager = context.getPackageManager();
Field declaredField2 = packageManager.getClass().getDeclaredField(“mPM”);
declaredField2.setAccessible(true);
declaredField2.set(packageManager, newProxyInstance);
System.out.println(“PmsHook success.”);








 本文介绍了如何防止Android应用被破解,通过分析破解者的方法,如使用JADX进行逆向工程,以及他们如何动态代理IPackageManager以篡改签名。提出了三种防御策略:在attachBaseContext之前检查签名,检查Application是否被替换,以及检测IPackageManager是否被动态代理。同时提供了具体的Java代码示例来实现这些检测方法。
本文介绍了如何防止Android应用被破解,通过分析破解者的方法,如使用JADX进行逆向工程,以及他们如何动态代理IPackageManager以篡改签名。提出了三种防御策略:在attachBaseContext之前检查签名,检查Application是否被替换,以及检测IPackageManager是否被动态代理。同时提供了具体的Java代码示例来实现这些检测方法。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








