1、全新安装的vCenter6.7启动后页面提示503报错
1)如vCenter为全新部署,请在安装阶段1完成后,马上登陆vCenter系统,修改hosts配置,添加以下行
IP(实际使用) localhost photon-machine(主机名)
2)如已完成第2阶段部署,则操作同上,并重启vCenter。
2、日常使用中突发503报错
1)登陆vCenter检查日志存储空间使用情况
找到使用已达100%的目录,执行以下命令删除30天以前的文件,然后重启vCenter
find * -mtime +30 -exec rm {} \;
2)确认vCenter的证书是否到期
使用官方修改工具Fixsts.sh修复
#系统无法通过任何方法远程传输文件,只能按以下方法操作创建
创建并粘贴代码 vi fixsts.sh
授权 chmod +x fixsts.sh
执行 ./fixsts.sh
#!/bin/bash
# Copyright (c) 2020-2021 VMware, Inc. All rights reserved.
# VMware Confidential
#
# Run this from the affected PSC/VC
#
# NOTE: This works on external and embedded PSCs
# This script will do the following
# 1: Regenerate STS certificate
#
# What is needed?
# 1: Offline snapshots of VCs/PSCs
# 2: SSO Admin Password
NODETYPE=$(cat /etc/vmware/deployment.node.type)
if [ "$NODETYPE" = "management" ]; then
echo "Detected this node is a vCenter server with external PSC."
echo "Please run this script from a vCenter with embedded PSC, or an external PSC"
exit 1
fi
if [ "$NODETYPE" = "embedded" ] && [ ! -f /usr/lib/vmware-vmdir/sbin/vmdird ]; then
echo "Detected this node is a vCenter gateway"
echo "Please run this script from a vCenter with embedded PSC, or an external PSC"
exit 1
fi
echo "NOTE: This works on external and embedded PSCs"
echo "This script will do the following"
echo "1: Regenerate STS certificate"
echo "What is needed?"
echo "1: Offline snapshots of VCs/PSCs"
echo "2: SSO Admin Password"
echo "IMPORTANT: This script should only be run on a single PSC per SSO domain"
mkdir -p /tmp/vmware-fixsts
SCRIPTPATH="/tmp/vmware-fixsts"
LOGFILE="$SCRIPTPATH/fix_sts_cert.log"
echo "==================================" | tee -a $LOGFILE
echo "Resetting STS certificate for $HOSTNAME started on $(date)" | tee -a $LOGFILE
echo ""| tee -a $LOGFILE
echo ""
DN=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\Services\vmdir]' | grep dcAccountDN | awk '{$1=$2=$3="";print $0}'|tr -d '"'|sed -e 's/^[ \t]*//')
echo "Detected DN: $DN" | tee -a $LOGFILE
PNID=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\Services\vmafd\Parameters]' | grep PNID | awk '{print $4}'|tr -d '"')
echo "Detected PNID: $PNID" | tee -a $LOGFILE
PSC=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\Services\vmafd\Parameters]' | grep DCName | awk '{print $4}'|tr -d '"')
echo "Detected PSC: $PSC" | tee -a $LOGFILE
DOMAIN=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\Services\vmafd\Parameters]' | grep DomainName | awk '{print $4}'|tr -d '"')
echo "Detected SSO domain name: $DOMAIN" | tee -a $LOGFILE
SITE=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\Services\vmafd\Parameters]' | grep SiteName | awk '{print $4}'|tr -d '"')
MACHINEID=$(/usr/lib/vmware-vmafd/bin/vmafd-cli get-machine-id --server-name localhost)
echo "Detected Machine ID: $MACHINEID" | tee -a $LOGFILE
IPADDRESS=$(ifconfig | grep eth0 -A1 | grep "inet addr" | awk -F ':' '{print $2}' | awk -F ' ' '{print $1}')
echo "Detected IP Address: $IPADDRESS" | tee -a $LOGFILE
DOMAINCN="dc=$(echo "$DOMAIN" | sed 's/\./,dc=/g')"
echo "Domain CN: $DOMAINCN"
ADMIN="cn=administrator,cn=users,$DOMAINCN"
USERNAME="administrator@${DOMAIN^^}"
ROOTCERTDATE=$(openssl x509 -in /var/lib/vmware/vmca/root.cer -text | grep "Not After" | awk -F ' ' '{print $7,$4,$5}')
TODAYSDATE=$(date +"%Y %b %d")
echo "#" > $SCRIPTPATH/certool.cfg
echo "# Template file for a CSR request" >> $SCRIPTPATH/certool.cfg
echo "#" >> certool.cfg
echo "# Country is needed and has to be 2 characters" >> $SCRIPTPATH/certool.cfg
echo "Country = DS" >> $SCRIPTPATH/certool.cfg
echo "Name = $PNID" >> $SCRIPTPATH/certool.cfg
echo "Organization = VMware" >> $SCRIPTPATH/certool.cfg
echo "OrgUnit = VMware" >> $SCRIPTPATH/certool.cfg
echo "State = VMware" >> $SCRIPTPATH/certool.cfg
echo "Locality = VMware" >> $SCRIPTPATH/certool.cfg
echo "IPAddress = $IPADDRESS" >> $SCRIPTPATH/certool.cfg
echo "Email = email@acme.com" >> $SCRIPTPATH/certool.cfg
echo "Hostname = $PNID" >> $SCRIPTPATH/certool.cfg
echo "==================================" | tee -a $LOGFILE
echo "==================================" | tee -a $LOGFILE
echo ""
echo "Detected Root's certificate expiration date: $ROOTCERTDATE" | tee -a $LOGFILE
echo "Detected today's date: $TODAYSDATE" | tee -a $LOGFILE
echo "==================================" | tee -a $LOGFILE
flag=0
if [[ $TODAYSDATE > $ROOTCERTDATE ]];
then
echo "IMPORTANT: Root certificate is expired, so it will be replaced" | tee -a $LOGFILE
flag=1
mkdir /certs && cd /certs
cp $SCRIPTPATH/certool.cfg /certs/vmca.cfg
/usr/lib/vmware-vmca/bin/certool --genselfcacert --outprivkey /certs/vmcacert.key --outcert /certs/vmcacert.crt --config /certs/vmca.cfg
/usr/lib/vmware-vmca/bin/certool --rootca --cert /certs/vmcacert.crt --privkey /certs/vmcacert.key
fi
echo "#" > $SCRIPTPATH/certool.cfg
echo "# Template file for a CSR request" >> $SCRIPTPATH/certool.cfg
echo "#" >> $SCRIPTPATH/certool.cfg
echo "# Country is needed and has to be 2 characters" >> $SCRIPTPATH/certool.cfg
echo "Country = DS" >> $SCRIPTPATH/certool.cfg
echo "Name = STS" >> $SCRIPTPATH/certool.cfg
echo "Organization = VMware" >> $SCRIPTPATH/certool.cfg
echo "OrgUnit = VMware" >> $SCRIPTPATH/certool.cfg
echo "State = VMware" >> $SCRIPTPATH/certool.cfg
echo "Locality = VMware" >> $SCRIPTPATH/certool.cfg
echo "IPAddress = $IPADDRESS" >> $SCRIPTPATH/certool.cfg
echo "Email = email@acme.com" >> $SCRIPTPATH/certool.cfg
echo "Hostname = $PNID" >> $SCRIPTPATH/certool.cfg
echo ""
echo "Exporting and generating STS certificate" | tee -a $LOGFILE
echo ""
cd $SCRIPTPATH
/usr/lib/vmware-vmca/bin/certool --server localhost --genkey --privkey=sts.key --pubkey=sts.pub
/usr/lib/vmware-vmca/bin/certool --gencert --cert=sts.cer --privkey=sts.key --config=$SCRIPTPATH/certool.cfg
openssl x509 -outform der -in sts.cer -out sts.der
CERTS=$(csplit -f root /var/lib/vmware/vmca/root.cer '/-----BEGIN CERTIFICATE-----/' '{*}' | wc -l)
openssl pkcs8 -topk8 -inform pem -outform der -in sts.key -out sts.key.der -nocrypt
i=1
until [ $i -eq $CERTS ]
do
openssl x509 -outform der -in root0$i -out vmca0$i.der
((i++))
done
echo ""
echo ""
read -s -p "Enter password for administrator@$DOMAIN: " DOMAINPASSWORD
echo ""
# Find the highest tenant credentials index
MAXCREDINDEX=1
while read -r line
do
INDEX=$(echo "$line" | tr -dc '0-9')
if [ $INDEX -gt $MAXCREDINDEX ]
then
MAXCREDINDEX=$INDEX
fi
done < <(/opt/likewise/bin/ldapsearch -h localhost -p 389 -b "cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" "(objectclass=vmwSTSTenantCredential)" cn | grep cn:)
# Sequentially search for tenant credentials up to max index and delete if found
echo "Highest tenant credentials index : $MAXCREDINDEX" | tee -a $LOGFILE
i=1
if [ ! -z $MAXCREDINDEX ]
then
until [ $i -gt $MAXCREDINDEX ]
do
echo "Exporting tenant $i to $SCRIPTPATH" | tee -a $LOGFILE
echo ""
ldapsearch -h localhost -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" -b "cn=TenantCredential-$i,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" > $SCRIPTPATH/tenantcredential-$i.ldif
if [ $? -eq 0 ]
then
echo "Deleting tenant $i" | tee -a $LOGFILE
ldapdelete -h localhost -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" "cn=TenantCredential-$i,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" | tee -a $LOGFILE
else
echo "Tenant $i not found" | tee -a $LOGFILE
echo ""
fi
((i++))
done
fi
echo ""
# Find the highest trusted cert chains index
MAXCERTCHAINSINDEX=1
while read -r line
do
INDEX=$(echo "$line" | tr -dc '0-9')
if [ $INDEX -gt $MAXCERTCHAINSINDEX ]
then
MAXCERTCHAINSINDEX=$INDEX
fi
done < <(/opt/likewise/bin/ldapsearch -h localhost -p 389 -b "cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" "(objectclass=vmwSTSTenantTrustedCertificateChain)" cn | grep cn:)
# Sequentially search for trusted cert chains up to max index and delete if found
echo "Highest trusted cert chains index: $MAXCERTCHAINSINDEX" | tee -a $LOGFILE
i=1
if [ ! -z $MAXCERTCHAINSINDEX ]
then
until [ $i -gt $MAXCERTCHAINSINDEX ]
do
echo "Exporting trustedcertchain $i to $SCRIPTPATH" | tee -a $LOGFILE
echo ""
ldapsearch -h localhost -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" -b "cn=TrustedCertChain-$i,cn=TrustedCertificateChains,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" > $SCRIPTPATH/trustedcertchain-$i.ldif
if [ $? -eq 0 ]
then
echo "Deleting trustedcertchain $i" | tee -a $LOGFILE
ldapdelete -h localhost -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" "cn=TrustedCertChain-$i,cn=TrustedCertificateChains,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" | tee -a $LOGFILE
else
echo "Trusted cert chain $i not found" | tee -a $LOGFILE
fi
echo ""
((i++))
done
fi
echo ""
i=1
echo "dn: cn=TenantCredential-1,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" > sso-sts.ldif
echo "changetype: add" >> sso-sts.ldif
echo "objectClass: vmwSTSTenantCredential" >> sso-sts.ldif
echo "objectClass: top" >> sso-sts.ldif
echo "cn: TenantCredential-1" >> sso-sts.ldif
echo "userCertificate:< file:sts.der" >> sso-sts.ldif
until [ $i -eq $CERTS ]
do
echo "userCertificate:< file:vmca0$i.der" >> sso-sts.ldif
((i++))
done
echo "vmwSTSPrivateKey:< file:sts.key.der" >> sso-sts.ldif
echo "" >> sso-sts.ldif
echo "dn: cn=TrustedCertChain-1,cn=TrustedCertificateChains,cn=$DOMAIN,cn=Tenants,cn=IdentityManager,cn=Services,$DOMAINCN" >> sso-sts.ldif
echo "changetype: add" >> sso-sts.ldif
echo "objectClass: vmwSTSTenantTrustedCertificateChain" >> sso-sts.ldif
echo "objectClass: top" >> sso-sts.ldif
echo "cn: TrustedCertChain-1" >> sso-sts.ldif
echo "userCertificate:< file:sts.der" >> sso-sts.ldif
i=1
until [ $i -eq $CERTS ]
do
echo "userCertificate:< file:vmca0$i.der" >> sso-sts.ldif
((i++))
done
echo ""
echo "Applying newly generated STS certificate to SSO domain" | tee -a $LOGFILE
/opt/likewise/bin/ldapmodify -x -h localhost -p 389 -D "cn=administrator,cn=users,$DOMAINCN" -w "$DOMAINPASSWORD" -f sso-sts.ldif | tee -a $LOGFILE
echo ""
echo "Replacement finished - Please restart services on all vCenters and PSCs in your SSO domain" | tee -a $LOGFILE
echo "==================================" | tee -a $LOGFILE
echo "IMPORTANT: In case you're using HLM (Hybrid Linked Mode) without a gateway, you would need to re-sync the certs from Cloud to On-Prem after following this procedure" | tee -a $LOGFILE
echo "==================================" | tee -a $LOGFILE
echo "==================================" | tee -a $LOGFILE
if [ $flag == 1 ]
then
echo "Since your Root certificate was expired and was replaced, you will need to replace your MachineSSL and Solution User certificates" | tee -a $LOGFILE
echo "You can do so following this KB: https://kb.vmware.com/s/article/2097936" | tee -a $LOGFILE
fi
根据提示输入信息。我这里没有截图就不重新生成证书了,但注意提示输入IP地址和NAME时分别 输入vcenter的IP和主机名。
3、主机无法与已启用 vSAN 的群集中的其他一个或多个节点进行通信
1)ESXI主机 管理--网络--虚拟交换机(非vsan)--安全--混杂模式--接收
4、无法加载vSan页面内容,原因是vCenter由6.5或以下版本升级到6.7产生的BUG,同样是STS的BUG导致证书不统一问题,通过fixsh.sh尝试修复,但问题没有解决,下面是其他方法:
#系统无法通过任何方法远程传输文件,只能按以下方法操作创建
1)使用vi方式在本地新建一个脚本 check-trust-anchors
2)把内容由本地计算机复制到这个脚本中
<<check-trust-anchors>>
#!/bin/bash
function setOptionColorize() {
RED=$(tput setaf 1)
GREEN=$(tput setaf 2)
YELLOW=$(tput setaf 3)
CYAN=$(tput setaf 6)
NORMAL=$(tput sgr0)
}
function unknownOption() {
echo "Unknown option '$2'. Please see '$1 --help' for usage and available options"
}
CURRENT_SERVICE_ID=''
SHOW_SERVICE_IDS=0
SHOW_ENDPOINTS=0
SHOW_DUPLICATE_ENDPOINTS=0
LIVE_CHECK=0
VIEW_MACHINE_SSL=0
DEBUG=0
FIX=0
TP_ALGORITHM="sha1"
TP_REGEX_ITER="19"
CERT_TEXT=0
CERT_COUNT=1
RED=''
GREEN=''
YELLOW=''
CYAN=''
NORMAL=''
LSTOOL_FILE='lstool.txt'
if [[ ${LIVE_CHECK} -gt 0 ]]; then
VC_VERSION=$(grep 'CLOUDVM_VERSION:' /etc/vmware/.buildInfo | awk -F':' '{print $NF}' | awk -F'.' '{print $1}')
else
VC_VERSION=$(grep 'CLOUDVM_VERSION:' ../etc/vmware/.buildInfo | awk -F':' '{print $NF}' | awk -F'.' '{print $1}')
fi
if [[ ${VC_VERSION} -eq 7 ]]; then
LS_PORT='7090'
LSTOOL_SCRIPT='/usr/lib/vmware-lookupsvc/tools/lstool.py'
LSUPDATE_SCRIPT='/usr/lib/vmware-lookupsvc/tools/ls_update_certs.py'
else
LS_PORT='7080'
LSTOOL_SCRIPT='/usr/lib/vmidentity/tools/scripts/lstool.py'
LSUPDATE_SCRIPT='/usr/lib/vmidentity/tools/scripts/ls_update_certs.py'
fi
if [ -f /usr/bin/ldapsearch ]; then
LDAPSEARCH='/usr/bin/ldapsearch'
else
LDAPSEARCH='/opt/likewise/bin/ldapsearch'
fi
if [ "$#" -ge 1 ]; then
for arg in "$@"; do
case ${arg} in
-h|--help)
echo "SSL Trust Anchor Verification Script"
echo "Usage: $0 [options]"
echo "Options:"
echo " -s | --show-service-ids Shows the Service IDs that are using a particular SSL certificate."
echo " -e | --show-endpoints Shows the Endpoing URIs that are using a particular SSL certificate."
echo " -c | --colorize Colorizes text for quick identification of Subject field, SHA1 Fingerprint, or"
echo " expired certificates. Do not use if passing output to a paginator or file."
echo " -l | --live-check Used in conjunction with the '-m|--machine-ssl' option, will indicate the script"
echo " is running on a live system, and will display current Machine SSL certificates"
echo " for all nodes with endpoints in the current SSO Site."
echo " -m | --machine-ssl Will display information on the current Machine SSL ceritifcate. Cannot be run on"
echo " a support bundle from an external Platform Services Controller."
echo " -t | --cert-text Will provide full output of each certificate similar to 'openssl x509 -text'"
echo " -f | --fix Will prompt for SSO credentials, thumbprint of a trust anchor cert to update, and the IP/FQDN"
echo " of a node to update."
echo " -d | --debug Will include the raw certificate hash to see if there are any extra characters"
echo " (sometimes the lstool.py script has connection issues and STDERR gets randomly"
echo " inserted in the output)."
echo " -h | --help Prints this help menu."
echo " -2 | --sha256 Outputs the SHA256 thumbprint of the certificates instead of the SHA1 thumbprint"
echo $'\n'"Parses the output of the following command from the Platform Services Controller:"
echo "${LSTOOL_SCRIPT} list --url http://localhost:${LS_PORT}/lookupservice/sdk 2>/dev/null"
echo $'\n'"Can be run from the 'commands/' directory of a support bundle, or live on a PSC node"
exit
;;
--show-service-ids)
SHOW_SERVICE_IDS=1
;;
--show-endpoints)
SHOW_ENDPOINTS=1
;;
--colorize)
setOptionColorize
;;
--live-check)
LIVE_CHECK=1
;;
--machine-ssl)
VIEW_MACHINE_SSL=1
;;
--debug)
DEBUG=1
;;
--cert-text)
CERT_TEXT=1
;;
--fix)
FIX=1
;;
--sha256)
TP_ALGORITHM="sha256"
TP_REGEX_ITER="31"
;;
-[seclmfdt2]*)
OPT=$(echo "z${arg}" | sed 's/z-//')
for (( i=0; i<${#OPT}; i++ )); do
case ${OPT:$i:1} in
s)
SHOW_SERVICE_IDS=1
;;
e)
SHOW_ENDPOINTS=1
;;
c)
setOptionColorize
;;
d)
DEBUG=1
;;
l)
LIVE_CHECK=1
;;
m)
VIEW_MACHINE_SSL=1
;;
t)
CERT_TEXT=1
;;
f)
FIX=1
;;
2)
TP_ALGORITHM="sha256"
TP_REGEX_ITER="31"
;;
*)
unknownOption $0 '-${OPT:$i:1}'
exit
;;
esac
done
;;
*)
unknownOption $0 ${arg}
exit
;;
esac
done
fi
if [[ ${LIVE_CHECK} -eq 0 ]]; then
if [ ! -f ${LSTOOL_FILE} ]; then
if [ ! -f "python.exe_VMWARE_CIS_HOMEVMwareIdentityServiceslstoolscriptslstoolpy-list---url-httplocalhost7080lo[...].txt" ]; then
echo "${YELLOW}No output from 'lstool.py list' found in this bundle."
else
LSTOOL_FILE='python.exe_VMWARE_CIS_HOMEVMwareIdentityServiceslstoolscriptslstoolpy-list---url-httplocalhost7080lo[...].txt'
fi
fi
if [ -f ../etc/vmware/deployment.node.type ]; then
NODE_TYPE=$(cat ../etc/vmware/deployment.node.type)
elif [ -f ../ProgramData/VMware/vCenterServer/cfg/deployment.node.type ]; then
NODE_TYPE=$(cat ../ProgramData/VMware/vCenterServer/cfg/deployment.node.type)
fi
else
NODE_TYPE=$(cat /etc/vmware/deployment.node.type)
if [ ${NODE_TYPE} == 'management' ]; then
echo "${YELLOW}Operation not supported on a Management Node. Please run this live on a PSC node. Exiting...${NORMAL}"
exit
fi
if [ ! -f ${LSTOOL_FILE} ]; then LSTOOL_FILE='/tmp/lstool.txt'; fi
echo "${YELLOW}No 'lstool.txt' file found in this directory. Dumping service registrations to ${LSTOOL_FILE}...${NORMAL}"
${LSTOOL_SCRIPT} list --url http://localhost:${LS_PORT}/lookupservice/sdk 2>/tmp/lstool_stderr > ${LSTOOL_FILE}
fi
DATA=$(cat ${LSTOOL_FILE} | grep -vE '^[0-9]{4}-[0-9]{2}-[0-9]{2}' | grep -E 'Service ID:|URL:|SSL trust:|^[0-9A-Za-z/\+]' | tr -d ' ' | tr -d '\n' | tr -d '\t' | tr -d '\r\n' | sed -e 's/ServiceID:/\nServiceID:/g' -e 's/URL:/\nURL:/g' -e 's/SSLtrust:/\nSSLtrust:/g')
TRUST_ANCHORS=$(echo "${DATA}" | grep 'SSLtrust' | sed -e 's/SSLtrust://g' | sort | uniq)
for RAW_HASH in ${TRUST_ANCHORS}; do
echo "${CYAN}-----Endpoint Certificate ${CERT_COUNT}-----${NORMAL}"
if [[ ${RAW_HASH} =~ [0-9]{4}-[0-9]{2}-[0-9]{2} ]]; then
echo "${RED}Malformed hash detected${NORMAL}"
BAD=$(echo "${RAW_HASH}" | grep -oE '[0-9]{4}-[0-9]{2}-[0-9]{2}(.)+')
HASH="$(echo "${RAW_HASH}" | sed -e 's/${BAD}//')"
CHARS=${#HASH}
MOD=$((${CHARS} % 4))
case ${MOD} in
3)
HASH="${HASH}="
;;
2)
HASH="${HASH}=="
;;
esac
else
HASH=${RAW_HASH}
fi
CURRENT_CERT="-----BEGIN CERTIFICATE-----"$'\n'
CURRENT_CERT+=$(echo ${HASH} | fold -c64)
CURRENT_CERT+=$'\n'"-----END CERTIFICATE-----"
if echo "${CURRENT_CERT}" | openssl x509 -text > /dev/null 2>&1; then
if [[ ${CERT_TEXT} -gt 0 ]]; then
CURRENT_CERT_INFO=$(echo "${CURRENT_CERT}" | openssl x509 -text -noout -fingerprint -${TP_ALGORITHM} | sed -e 's/SHA[0-9]* Fingerprint/\t&/g' -e "s/Subject:/${GREEN}&${NORMAL}/g" -e "s/[[:xdigit:]]\{2\}\(:[[:xdigit:]]\{2\}\)\{${TP_REGEX_ITER}\}/${YELLOW}&${NORMAL}/g" -e "s/X509v3 Subject Alternative Name/${GREEN}&${NORMAL}/g")
echo "${CURRENT_CERT_INFO}"
else
CURRENT_CERT_INFO=$(echo "${CURRENT_CERT}" | openssl x509 -text -noout -fingerprint -${TP_ALGORITHM} | grep -E 'Issuer:|Subject:|Validity|Not Before:|Not After :|Fingerprint' | sed -e 's/SHA[0-9]* Fingerprint/\t&/g' -e "s/Subject:/${GREEN}&${NORMAL}/g" -e "s/[[:xdigit:]]\{2\}\(:[[:xdigit:]]\{2\}\)\{${TP_REGEX_ITER}\}/${YELLOW}&${NORMAL}/g")
echo "Certificate Info:"
if echo "${CURRENT_CERT}" | openssl x509 -noout -checkend 0; then
echo "${CURRENT_CERT_INFO}"
else
echo "${CURRENT_CERT_INFO}" | sed -e "s/Not Before/${RED}&/"
fi
if [[ ${DEBUG} -gt 0 ]]; then echo $'\t'"Certificate Hash: ${HASH}"; fi
fi
else
echo "${RED}Unable to parse certificate hash${NORMAL}"
if [[ ${DEBUG} -gt 0 ]]; then echo "${HASH}"; fi
fi
if [[ ${SHOW_SERVICE_IDS} -gt 0 ]]; then
REGEX_HASH=$(echo "${RAW_HASH}" | sed -e 's/\+/\\+/g' -e 's/\$/\\$/g')
FOUND_SERVICE_IDS=''
for line in $(echo "${DATA}" | grep -vE '^URL:' | uniq | grep -E "ServiceID|${REGEX_HASH}" | grep -B1 ${RAW_HASH}); do
if [[ "${line}" =~ ^ServiceID ]]; then
CURRENT_SERVICE_ID=$(echo "${line}" | sed -e 's/ServiceID://g')
elif $(echo "${line}" | grep ${RAW_HASH} > /dev/null); then
if [ -z "${FOUND_SERVICE_IDS}" ]; then
FOUND_SERVICE_IDS=$'\t'"${CURRENT_SERVICE_ID}"
else
FOUND_SERVICE_IDS+=$'\n\t'"${CURRENT_SERVICE_ID}"
fi
fi
done
NUM_FOUND_SERVICE_IDS=$(echo "${FOUND_SERVICE_IDS}" | sort | uniq | wc -l)
echo "Service IDs (${NUM_FOUND_SERVICE_IDS}):"
echo "${FOUND_SERVICE_IDS}" | sort | uniq
fi
if [[ ${SHOW_ENDPOINTS} -gt 0 ]]; then
ENDPOINTS=$(echo "${DATA}" | grep -vE '^ServiceID' | grep -B1 ${RAW_HASH} | grep -E '^URL:' | sed -e 's/URL:/\t/g' | sort | uniq)
NUM_ENDPOINTS=$(echo "${ENDPOINTS}" | wc -l)
echo "Endpoints (${NUM_ENDPOINTS}):"
echo "${ENDPOINTS}"
fi
echo "${CYAN}--------------------------------${NORMAL}"
((++CERT_COUNT))
done
if [[ ${VIEW_MACHINE_SSL} -gt 0 ]]; then
if [[ ${LIVE_CHECK} -eq 0 ]]; then
if [ "${NODE_TYPE}" = 'infrastructure' ]; then
echo $'\n'"${YELLOW}The Machine SSL certificate is not included in an external PSC support bundle.${NORMAL}"
else
if [ -f ../etc/vmware-vpx/ssl/rui.crt ]; then
MACHINE_SSL_FILE='../etc/vmware-vpx/ssl/rui.crt'
elif [ -f ../ProgramData/VMware/vCenterServer/cfg/vmware-vpx/ssl/rui.crt ]; then
MACHINE_SSL_FILE='../ProgramData/VMware/vCenterServer/cfg/vmware-vpx/ssl/rui.crt'
fi
if [ ! -z ${MACHINE_SSL_FILE} ]; then
echo $'\n'"${CYAN}-----Machine SSL Certificate-----${NORMAL}"
CURRENT_MACHINE_SSL_CERT_INFO=$(cat ${MACHINE_SSL_FILE} | openssl x509 -text -noout -fingerprint -${TP_ALGORITHM} | grep -E 'Issuer:|Subject:|Validity|Not Before:|Not After :|Fingerprint' | sed -e 's/SHA[0-9]* Fingerprint/\t&/g' -e "s/Subject:/${GREEN}&${NORMAL}/g" -e "s/[[:xdigit:]]\{2\}\(:[[:xdigit:]]\{2\}\)\{${TP_REGEX_ITER}\}/${YELLOW}&${NORMAL}/g")
echo "Certificate Info:"
if cat "${MACHINE_SSL_FILE}" | openssl x509 -noout -checkend 0; then
echo "${CURRENT_MACHINE_SSL_CERT_INFO}"
else
echo "${CURRENT_MACHINE_SSL_CERT_INFO}" | sed -e "s/Not Before/${RED}&/"
fi
echo "${CYAN}---------------------------------${NORMAL}"
else
echo $'\n'"${YELLOW}Unable to locate the Machine SSL certificate file in the support bundle.${NORMAL}"
fi
fi
else
SSO_DOMAIN=$(/usr/lib/vmware-vmafd/bin/vmafd-cli get-domain-name --server-name localhost)
SSO_SITE=$(/usr/lib/vmware-vmafd/bin/vmafd-cli get-site-name --server-name localhost)
VMDIR_DC_BRANCH="dc=$(echo ${SSO_DOMAIN} | sed 's/\./,dc=/g')"
VMDIR_MACHINE_PASSWORD=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\services\vmdir]' | grep dcAccountPassword | awk -F" " '{print $NF}' | awk '{print substr($0,2,length($0)-2)}' | sed -e 's/\\"/"/g' -e 's/\\\\/\\/g' | tr -d '\n' > /tmp/.vmdir_machine_account_password; chmod go-r /tmp/.vmdir_machine_account_password)
VMDIR_MACHINE_ACCOUNT_DN=$(/opt/likewise/bin/lwregshell list_values '[HKEY_THIS_MACHINE\services\vmdir]' | grep '"dcAccountDN"' | awk -F" " '{print $NF}' | awk '{print substr($0,2,length($0)-2)}')
SITE_NODES=$(${LDAPSEARCH} -LLL -h localhost -p 389 -b "cn=ServiceRegistrations,cn=LookupService,cn=${SSO_SITE},cn=Sites,cn=Configuration,${VMDIR_DC_BRANCH}" -D "${VMDIR_MACHINE_ACCOUNT_DN}" -y /tmp/.vmdir_machine_account_password "(objectclass=vmwLKUPEndpointRegistration)" vmwLKUPURI | grep '^vmwLKUPURI' | sed -e 's/vmwLKUPURI://g' | awk -F'/' '{print $3}' | awk -F':' '{print $1}' | sort | uniq -i | grep -v localhost)
rm /tmp/.vmdir_machine_account_password
printf '\n'
for node in ${SITE_NODES}; do
echo "${CYAN}-----Machine SSL Certificate-----${NORMAL}"
echo "${CYAN}${node}${NORMAL}"
CURRENT_MACHINE_SSL_CERT_INFO=$(echo | openssl s_client -connect ${node}:443 2>/dev/null | openssl x509 -text -noout -fingerprint -${TP_ALGORITHM} | grep -E 'Issuer:|Subject:|Validity|Not Before:|Not After :|Fingerprint' | sed -e 's/SHA[0-9]* Fingerprint/\t&/g' -e "s/Subject:/${GREEN}&${NORMAL}/g" -e "s/[[:xdigit:]]\{2\}\(:[[:xdigit:]]\{2\}\)\{${TP_REGEX_ITER}\}/${YELLOW}&${NORMAL}/g")
echo "Certificate Info:"
if echo | openssl s_client -connect ${node}:443 2>/dev/null | openssl x509 -noout -checkend 0; then
echo "${CURRENT_MACHINE_SSL_CERT_INFO}"
else
echo "${CURRENT_MACHINE_SSL_CERT_INFO}" | sed -e "s/Not Before/${RED}&/"
fi
echo "${CYAN}---------------------------------${NORMAL}"
done
fi
fi
if [[ ${FIX} -gt 0 ]]; then
if [[ ${LIVE_CHECK} -gt 0 ]]; then
if [ ! -f ${LSUPDATE_SCRIPT} ]; then
echo $'\n'"${YELLOW}The ${LSUPDATE_SCRIPT} script could not be found. Please ensure you are running this from a PSC.${NORMAL}"
else
echo $'\n'"${CYAN}SSL Trust Anchor Repair${NORMAL}"
echo "${CYAN}---------------------------------${NORMAL}"
echo "This process will attempt to update the SSL trust anchors for Lookup Service registrations using native Lookup Service libraries. These changes should propagate to all PSCs in the SSO domain."
echo $'\n'"${YELLOW}It is strongly recommended that you take offline snapshots of all PSCs in the SSO domain before proceeding.${NORMAL}"
read -p $'\n'"Proceed with updating trust anchors? [Y/N]: " PROCEED
if [ -z ${PROCEED} ]; then PROCEED_FIX="n"; else PROCEED_FIX=$(echo ${PROCEED} | awk '{print tolower(substr($0,0,1))}'); fi
if [ ${PROCEED_FIX} == "y" ]; then
SSO_DOMAIN=$(/usr/lib/vmware-vmafd/bin/vmafd-cli get-domain-name --server-name localhost)
read -p $'\n'"Enter SSO admin [administrator@${SSO_DOMAIN}]: " LOGIN
if [ -z ${LOGIN} ]; then LOGIN="administrator@${SSO_DOMAIN}"; fi
read -s -p "Enter password for ${LOGIN}: " PASSWORD_INPUT
PASSWORD=$(echo ${PASSWORD_INPUT} | sed "s/'/'\\\''/g")
read -p $'\n'"Enter fingerprint of trust anchor(s) to update: " FINGERPRINT
read -p "Enter the FQDN of the node to update: " NODE_FQDN
if echo 'y' | openssl s_client -connect ${NODE_FQDN}:443 2>/dev/null | openssl x509 > /tmp/machine-ssl.crt; then
if ! ${LSUPDATE_SCRIPT} --url http://localhost:${LS_PORT}/lookupservice/sdk 2>/tmp/ls_update_certs.stderr --fingerprint ${FINGERPRINT} --certfile /tmp/machine-ssl.crt --user ${LOGIN} --password $(eval echo "'${PASSWORD}'"); then
echo $'\n'"${YELLOW}The ls_update_certs.py script encountered an error."
echo $'\n'"Please refer to /tmp/ls_update_certs.stderr for more information.${NORMAL}"
fi
else
echo $'\n'"${YELLOW}Unable to obtain SSL certificate from ${NODE_FQDN}. Exiting..."
fi
else
echo $'\n'"Operation aborted. Exiting..."
fi
fi
else
echo $'\n'"${YELLOW}Fixing trust anchors can only be done on a live system.${NORMAL}"
fi
fi
3)chmod +x check-trust-anchors
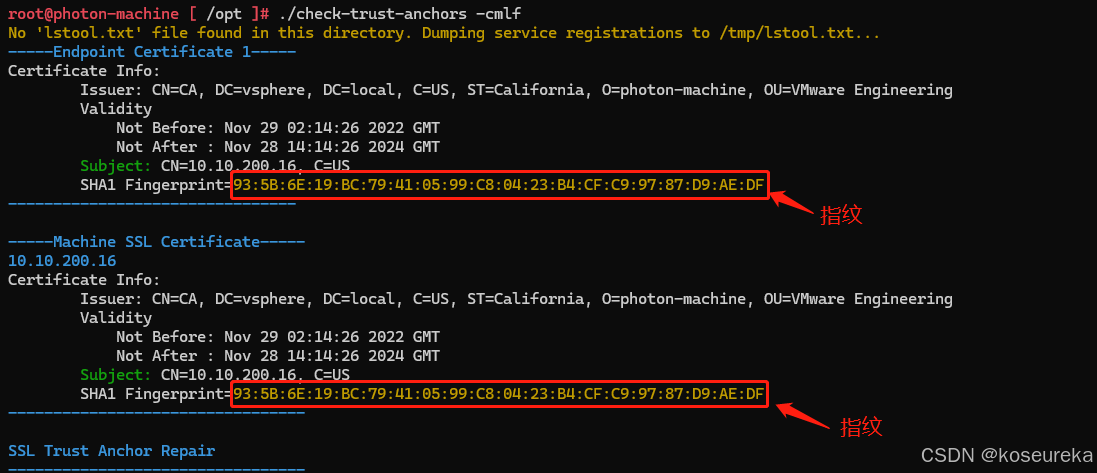
4)执行 ./check-trust-anchors -cmlf #这里会检测现在的数据,有可能会出现一种情况就是各个节点的SHA1指纹不一样
5)选择Y 、输入SSO账号:administrator@vsphere.local 、 输入SSO密码
6)提示输入一个指纹,我使用的是上图获取的指纹 :93:5B:6E:19:BC:79:41:05:99:C8:04:23:B4:CF:C9:97:87:D9:AE:DF (不要直接复制使用,每台VC的情况不一样)
7)等待完成更新修复即可




















 3万+
3万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








