
使用stegsolve 扫描
一直按“-->”,直到出现
使用QR工具扫码 工具
03F30D0A79CB05586300000000000000000100000040000000730D0000006400008400005A000064010053280200000063000000000300000016000000430000007378000000640100640200640300640400640500640600640700640300640800640900640A00640600640B00640A00640700640800640C00640C00640D00640E00640900640F006716007D00006410007D0100781E007C0000445D16007D02007C01007400007C0200830100377D0100715500577C010047486400005328110000004E6966000000696C00000069610000006967000000697B000000693300000069380000006935000000693700000069300000006932000000693400000069310000006965000000697D000000740000000028010000007403000000636872280300000074030000007374727404000000666C6167740100000069280000000028000000007304000000312E7079520300000001000000730A0000000001480106010D0114014E280100000052030000002800000000280000000028000000007304000000312E707974080000003C6D6F64756C653E010000007300000000
观察为十六进制
保存为txt放到winhex winhex下载
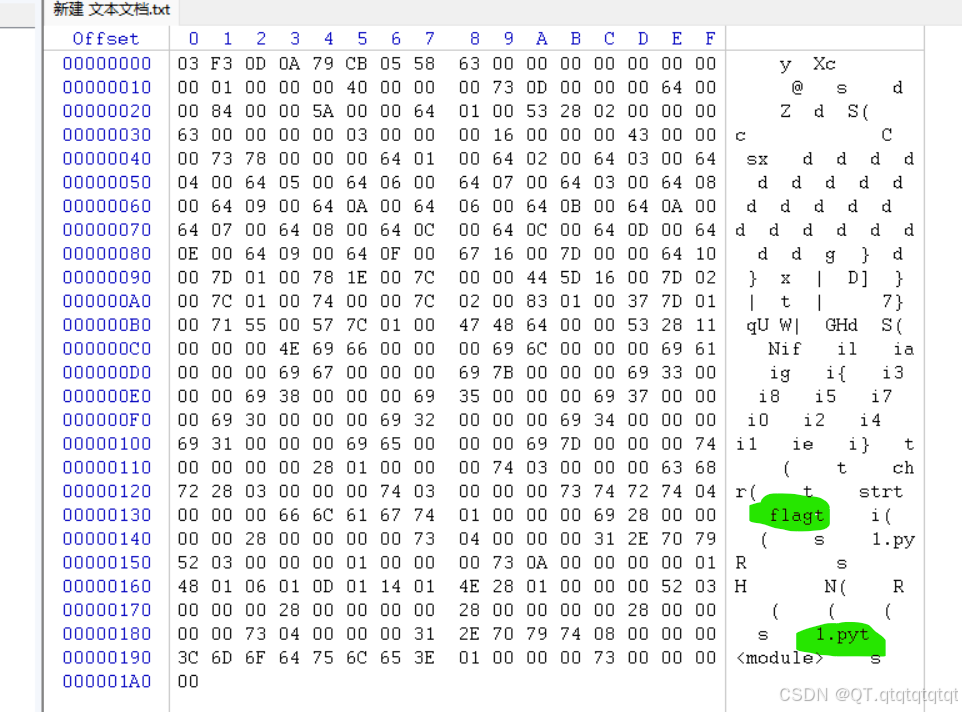
观察推测为pyc文件(py的编译文件),修改txt文件后缀名为pyc
使用反编译器EasyPythonDecompiler 安装
得到一个pyc_dis文件
修改pyc_dis文件后缀名为py
通过编译器打开(此处用vscode)
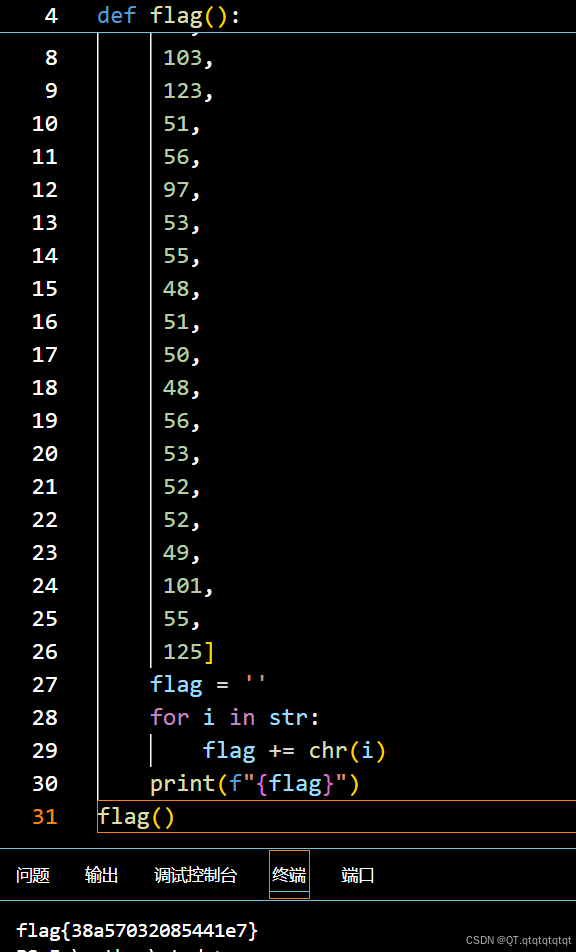
添加了两行代码运行即可得到flag
























 2503
2503

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








