kerbros的服务端执行即可。
[root@hadoop01 ~]# chkconfig krb5kdc on
[root@hadoop01 ~]# chkconfig kadmin on
[root@hadoop01 ~]# service krb5kdc start
[root@hadoop01 ~]# service kadmin start
[root@hadoop01 ~]# service krb5kdc status
1.3.6.3 kerberos的管理员创建
在kerbros服务端执行如下命令。
kadmin.local输入后,,添加规则:addprinc admin/admin@HIVE.COM。
[root@hadoop01 ~]# kadmin.local
Authenticating as principal root/admin@HIVE.COM with password.
继续如下图的填写:
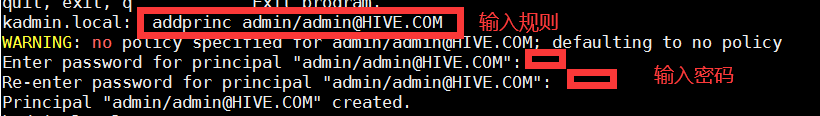
输入规则和密码,,两次密码相同即可,我是用的是root。
最后使用q、quit或者exist退出即可。
第二章 hadoop集群配置Kerbros
一些概念:
Kerberos principal用于在kerberos加密系统中标记一个唯一的身份。
kerberos为kerberos principal分配tickets使其可以访问由kerberos加密的hadoop服务。
对于hadoop,principals的格式为username/fully.qualified.domain.name@YOUR-REALM.COM.
keytab是包含principals和加密principal key的文件。 keytab文件对于每个host是唯一的,因为key中包含hostname。keytab文件用于不需要人工交互和保存纯文本密码,实现到kerberos上验证一个主机上的principal。 因为服务器上可以访问keytab文件即可以以principal的身份通过kerberos的认证,所以,keytab文件应该被妥善保存,应该只有少数的用户可以访问。
hive配置kerberos的前提是Hadoop集群已经配置好Kerberos,因此我们先来配置Hadoop集群的认证。
2.1 添加用户
如下的创建用户,密码都是用户名。可以随意设置。
#创建hadoop用户
[root@hadoop01 hadoop]# useradd hadoop
[root@hadoop01 hadoop]# passwd hadoop
[root@hadoop02 hadoop]# useradd hadoop
[root@hadoop02 hadoop]# passwd hadoop
[root@hadoop03 hadoop]# useradd hadoop
[root@hadoop03 hadoop]# passwd hadoop
#新建用户yarn,其中需设定userID<1000,命令如下:
[root@hadoop01 ~]# useradd -u 502 yarn -g hadoop
#并使用passwd命令为新建用户设置密码
[root@hadoop01 ~]# passwd yarn
passwd yarn 输入新密码
#创建hdfs用户
[root@hadoop01 hadoop]# useradd hdfs -g hadoop
[root@hadoop01 hadoop]# passwd hdfs
[root@hadoop02 hadoop]# useradd hdfs -g hadoop
[root@hadoop02 hadoop]# passwd hdfs
[root@hadoop03 hadoop]# useradd hdfs -g hadoop
[root@hadoop03 hadoop]# passwd hdfs
#创建HTTP用户
[root@hadoop01 hadoop]# useradd HTTP
[root@hadoop01 hadoop]# passwd HTTP
[root@hadoop02 hadoop]# useradd HTTP
[root@hadoop02 hadoop]# passwd HTTP
[root@hadoop03 hadoop]# useradd HTTP
[root@hadoop03 hadoop]# passwd HTTP
2.2 创建 kerberos的普通用户及密钥文件,为配置 YARN kerberos security 时,各节点可以相互访问用
在服务端节点的root用户下分别执行以下命令:
[root@hadoop01 ~]# cd /var/kerberos/krb5kdc/
#登录管理用户
[root@hadoop01 krb5kdc]# kadmin.local
#创建用户
addprinc -randkey yarn/hadoop01@HIVE.COM
addprinc -randkey yarn/hadoop02@HIVE.COM
addprinc -randkey yarn/hadoop03@HIVE.COM
addprinc -randkey hdfs/hadoop01@HIVE.COM
addprinc -randkey hdfs/hadoop02@HIVE.COM
addprinc -randkey hdfs/hadoop03@HIVE.COM
addprinc -randkey HTTP/hadoop01@HIVE.COM
addprinc -randkey HTTP/hadoop02@HIVE.COM
addprinc -randkey HTTP/hadoop03@HIVE.COM
#生成密钥文件(生成到当前路径下)
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k yarn.keytab yarn/hadoop01@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k yarn.keytab yarn/hadoop02@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k yarn.keytab yarn/hadoop03@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k HTTP.keytab HTTP/hadoop01@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k HTTP.keytab HTTP/hadoop02@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k HTTP.keytab HTTP/hadoop03@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k hdfs-unmerged.keytab hdfs/hadoop01@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k hdfs-unmerged.keytab hdfs/hadoop02@HIVE.COM"
[root@hadoop01 krb5kdc]# kadmin.local -q "xst -k hdfs-unmerged.keytab hdfs/hadoop03@HIVE.COM"
#合并成一个keytab文件,rkt表示展示,wkt表示写入
[root@hadoop01 krb5kdc]# ktutil
ktutil: rkt hdfs-unmerged.keytab
ktutil: rkt HTTP.keytab
ktutil: rkt yarn.keytab
ktutil: wkt hdfs.keytab
ktutil: q
注意:ktutil:以后面的是输入的。
#查看
[root@hadoop01 krb5kdc]# klist -ket hdfs.keytab
Keytab name: FILE:hdfs.keytab
KVNO Timestamp Principal
---- ------------------- ------------------------------------------------------
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (aes128-cts-hmac-sha1-96)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (des3-cbc-sha1)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (arcfour-hmac)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (camellia256-cts-cmac)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (camellia128-cts-cmac)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (des-hmac-sha1)
3 04/14/2020 15:48:21 hdfs/hadoop01@HIVE.COM (des-cbc-md5)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (aes128-cts-hmac-sha1-96)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (des3-cbc-sha1)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (arcfour-hmac)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (camellia256-cts-cmac)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (camellia128-cts-cmac)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (des-hmac-sha1)
3 04/14/2020 15:48:21 hdfs/hadoop02@HIVE.COM (des-cbc-md5)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (aes128-cts-hmac-sha1-96)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (des3-cbc-sha1)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (arcfour-hmac)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (camellia256-cts-cmac)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (camellia128-cts-cmac)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (des-hmac-sha1)
8 04/14/2020 15:48:21 HTTP/hadoop03@HIVE.COM (des-cbc-md5)
6 04/14/2020 15:48:21 HTTP/hadoop01@HIVE.COM (aes128-cts-hmac-sha1-96)
6 04/14/2020 15:48:21 HTTP/hadoop01@HIVE.COM (des3-cbc-sha1)
6 04/14/2020 15:48:21 HTTP/hadoop01@HIVE.COM (arcfour-hmac)
6 04/14/2020 15:48:21 HTTP/hadoop01@HIVE.COM (camellia256-cts-cmac)
6 04/14/2020 15:48:21 HTTP/hadoop01@HIVE.COM (camellia1







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








