ARPSPOOF_DETECTOR
Watch value for gateway mac in the arp table
Nice and simple, but will not detect an attack if the tool is executed after the attack.
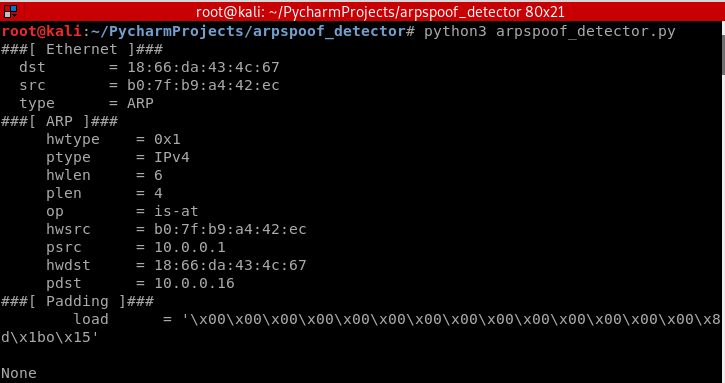
Analyze "is-at" ARP responses:
Check if IP is gateway IP.
Check if source mac is actually the gateway's mac.
This method will detect attacks even if the attack was launched before the execution of the tool.
#!/usr/bin/env python import scapy from scapy.layers.l2 import ARP from scapy.sendrecv import sniff def sniff(interface): scapy.sendrecv.sniff(iface=interface, store=False, prn=process_sniffed_packet) def process_sniffed_packet(packet): if packet.haslayer(ARP) and packet[ARP].op == 2: print(packet.show()) sniff("eth0")
Update the Python code to detect the real attack!
#!/usr/bin/env python import scapy from scapy.layers.l2 import ARP, Ether from scapy.sendrecv import sniff, srp def get_mac(ip): arp_request = ARP(pdst=ip) broadcast = Ether(dst="ff:ff:ff:ff:ff:ff") arp_request_broadcast = broadcast / arp_request answered_list = srp(arp_request_broadcast, timeout=1, verbose=False)[0] return answered_list[0][1].hwsrc def sniff(interface): scapy.sendrecv.sniff(iface=interface, store=False, prn=process_sniffed_packet) def process_sniffed_packet(packet): try: real_mac = get_mac(packet[ARP].psrc) response_mac = packet[ARP].hwsrc if real_mac != response_mac: print("[+] You are under attack!!") except IndexError: pass sniff("eth0")
























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








