一种是3gstudent分享的调用Nsa泄露的smbtouch-1.1.1.exe实现验证,另一种是参考巡风的poc。这里整合学习了下两种不同的方法。
import os
import fileinput
print "---This is Ms17010's tools for 139/445---"
#ip开始
BeginIP = raw_input(" [+] >输入开始ip:") #172.16.9.1
#ip终点
EndIP = raw_input(" [+] >输入终端ip:")
#Log file
fp = open('log.txt', 'w+')
#向Smbtouch-1.1.1.xml里面按照xml的格式文档写入默认127.0.0.1
OldIP = ' <value>127.0.0.1</value>'
TempIP = OldIP
print "------------------scaning----------------"
print ""
#切片操作
IP1 = BeginIP.split('.')[0]
IP2 = BeginIP.split('.')[1]
IP3 = BeginIP.split('.')[2]
IP4 = BeginIP.split('.')[-1]
EndIP_last = EndIP.split('.')[-1]
for i in range(int(IP4)-1,int(EndIP_last)):
ip = str(IP1+'.'+IP2+'.'+IP3+'.'+IP4)
int_IP4 = int(IP4)
int_IP4 += 1
IP4 = str(int_IP4)
NewIP= ' <value>'+ip+'</value>'
for line in fileinput.input('Smbtouch-1.1.1.xml',inplace=1):
print line.rstrip().replace(TempIP,NewIP)
TempIP = NewIP
Output = os.popen(r"Smbtouch-1.1.1.exe").read()
Output = Output[0:Output.find('<config',1)]
fp.writelines(Output)
Flag = Output.find('[-] Touch failed')
if Flag == -1 :
print '[+] Touch success: ' +ip
else:
print '[-] Touch failed: ' +ip
else:
fp.close( )
for line in fileinput.input('Smbtouch-1.1.1.xml',inplace=1):
print line.rstrip().replace(NewIP,OldIP)
前两天看到freebuf的关于《如何转换永恒之蓝(Eternalblue)的POC》
ms17-010 poc
#!/usr/bin/python
# coding: utf-8
'''
The poc is used to detecte MS17-010
'''
import binascii
import socket
import struct
import sys
import threading
negotiate_protocol_request = binascii.unhexlify(
"00000085ff534d4272000000001853c00000000000000000000000000000fffe00004000006200025043204e4554574f524b2050524f4752414d20312e3000024c414e4d414e312e30000257696e646f777320666f7220576f726b67726f75707320332e316100024c4d312e325830303200024c414e4d414e322e3100024e54204c4d20302e313200")
session_setup_request = binascii.unhexlify(
"00000088ff534d4273000000001807c00000000000000000000000000000fffe000040000dff00880004110a000000000000000100000000000000d40000004b000000000000570069006e0064006f007700730020003200300030003000200032003100390035000000570069006e0064006f007700730020003200300030003000200035002e0030000000")
tree_connect_request = binascii.unhexlify(
"00000060ff534d4275000000001807c00000000000000000000000000000fffe0008400004ff006000080001003500005c005c003100390032002e003100360038002e003100370035002e003100320038005c00490050004300240000003f3f3f3f3f00")
trans2_session_setup = binascii.unhexlify(
"0000004eff534d4232000000001807c00000000000000000000000000008fffe000841000f0c0000000100000000000000a6d9a40000000c00420000004e0001000e000d0000000000000000000000000000")
def main(ips):
ip = ips
if ip != "":
check_ip(ip)
if filename != "":
with open(filename, "r") as fp:
for line in fp:
semaphore.acquire()
ip_address = line.strip()
t = threading.Thread(target=threaded_check, args=(ip_address,))
t.start()
num_threads = 10
timeout = 10
filename = ""
print_lock = threading.Lock()
if len(sys.argv) == 5:
ip = sys.argv[1]
filename = sys.argv[2]
timeout = sys.argv[3]
num_threads = sys.argv[4]
semaphore = threading.BoundedSemaphore(value=num_threads)
else:
print "[!] >............... "
def print_status(ip, message):
global print_lock
with print_lock:
print "[*] [%s] %s" % (ip, message)
def check_ip(ip):
global negotiate_protocol_request, session_setup_request, tree_connect_request, trans2_session_setup, timeout, verbose
# Connect to socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(float(timeout) if timeout else None)
host = ip
port = 445
s.connect((host, port))
# Send/receive negotiate protocol request
print_status(ip, "正在准备协议!")
s.send(negotiate_protocol_request)
s.recv(1024)
# Send/receive session setup request
print_status(ip, "正在设置请求!")
s.send(session_setup_request)
session_setup_response = s.recv(1024)
# Extract user ID from session setup response
user_id = session_setup_response[32:34]
print_status(ip, "用户 ID = %s" % struct.unpack("<H", user_id)[0])
# Replace user ID in tree connect request packet
modified_tree_connect_request = list(tree_connect_request)
modified_tree_connect_request[32] = user_id[0]
modified_tree_connect_request[33] = user_id[1]
modified_tree_connect_request = "".join(modified_tree_connect_request)
# Send tree connect request
print_status(ip, "发送连接!!!")
s.send(modified_tree_connect_request)
tree_connect_response = s.recv(1024)
# Extract tree ID from response
tree_id = tree_connect_response[28:30]
print_status(ip, "Tree ID = %s" % struct.unpack("<H", tree_id)[0])
# Replace tree ID and user ID in trans2 session setup packet
modified_trans2_session_setup = list(trans2_session_setup)
modified_trans2_session_setup[28] = tree_id[0]
modified_trans2_session_setup[29] = tree_id[1]
modified_trans2_session_setup[32] = user_id[0]
modified_trans2_session_setup[33] = user_id[1]
modified_trans2_session_setup = "".join(modified_trans2_session_setup)
# Send trans2 sessions setup request
print_status(ip, "发送成功!正在返回!")
s.send(modified_trans2_session_setup)
final_response = s.recv(1024)
s.close()
# Check for 0x51 response to indicate DOUBLEPULSAR infection
if final_response[34] == "\x51":
with print_lock:
print("\033[0;31m%s\033[0m" % "[*] 存在:DOUBLEPULSAR !!!\n" )
else:
with print_lock:
print "[-] 不存在DOUBLEPULSAR !!!\n"
def threaded_check(ip_address):
global semaphore
try:
check_ip(ip_address)
except Exception as e:
with print_lock:
print "[错误] [%s] - %s" % (ip_address, e)
finally:
semaphore.release()
if __name__ == '__main__':
ip = '192.168.1.1'
main(ip)
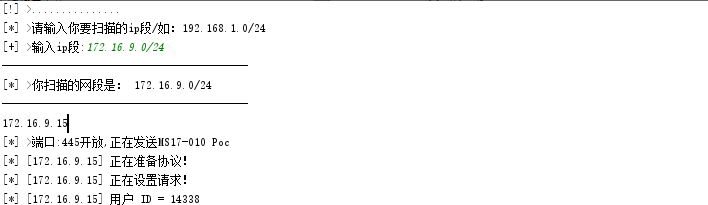
扫描这里使用IPy模块处理输入扫描网段和使用multiprocessing机制
# coding: utf-8
# by:adislj
import socket
from datetime import datetime
from multiprocessing.dummy import Pool as ThreadPool #多线程
import IPy
from MS17_010_poc import *
try:
print '[*] >请输入你要扫描的ip段/如:192.168.1.0/24'
remote_server = raw_input("[+] >输入ip段:") #172.16.9.0/24
ip_list = []
ips = IPy.IP(remote_server) #Class and tools for handling of IPv4 and IPv6 addresses and networks
for ipx in ips:
ip_list.append(ipx)
ip_list = ip_list[1:-1]
print '-' * 41
print '[*] >你扫描的网段是:', remote_server
print '-' * 41
socket.setdefaulttimeout(0.5)
except:
pass
def scan_port(ip_list):
try:
port_list = [445]
for port in port_list:
s = socket.socket(2, 1)
res = s.connect_ex((str(ip_list), port))
if res == 0: # 如果端口开启
if port == 445:
print ip_list
print '[*] >端口:{}开放,正在发送MS17-010 Poc'.format(port)
main(str(ip_list))
s.close()
else:
print '.' * 41
s.close()
except Exception, e:
print str(e.message)
if remote_server != '':
t1 = datetime.now()
pool = ThreadPool(processes=5)
results = pool.map(scan_port, ip_list)
pool.close()
pool.join()
else:
print '请输入ip段!'
exit(0)
print '[*] >MS17-010扫描完成时间:', datetime.now() - t1







 本文介绍了一种用于检测MS17-010漏洞的Python脚本工具,该工具通过调用Nsa泄露的smbtouch-1.1.1.exe进行验证,并实现了基于IP范围的批量扫描功能。
本文介绍了一种用于检测MS17-010漏洞的Python脚本工具,该工具通过调用Nsa泄露的smbtouch-1.1.1.exe进行验证,并实现了基于IP范围的批量扫描功能。
















 9182
9182

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








