jarvisoj_level3_x64
使用checksec查看:

只开启了栈不可执行,应该是jarvisoj_level3的x64版本,直接放进IDA中看吧:

主函数中直接给出了漏洞函数,跟进查看:
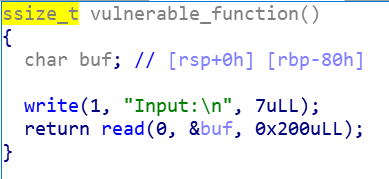
read()函数,存在栈溢出,和jarvisoj_level3的主要区别在栈上传参和寄存器传参。
exp:
from pwn import *
#start
# r = process("../buu/jarvisoj_level3_x64")
r = remote("node4.buuoj.cn",28760)
elf = ELF("../buu/jarvisoj_level3_x64")
libc  破解jarvisoj_level3_x64:栈溢出漏洞利用与exploit
破解jarvisoj_level3_x64:栈溢出漏洞利用与exploit





 本文详细讲述了在jarvisoj_level3_x64程序中发现的栈溢出漏洞,通过IDA进行分析,利用write函数进行参数篡改,最终实现从栈溢出到 libc 函数调用,完成系统调用和shellcode执行的过程。
本文详细讲述了在jarvisoj_level3_x64程序中发现的栈溢出漏洞,通过IDA进行分析,利用write函数进行参数篡改,最终实现从栈溢出到 libc 函数调用,完成系统调用和shellcode执行的过程。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章

















 615
615

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








