nmap典型用法
[root@node01 ~]# nmap 192.168.1.220`` ``Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-21 13:08 CST``Nmap scan report for 192.168.1.220``Host is up (0.00012s latency).``Not shown: 999 closed ports``PORT STATE SERVICE``22/tcp open ssh``MAC Address: 00:0C:29:C5:19:99 (VMware)`` ``Nmap done: 1 IP address (1 host up) scanned in 0.10 seconds
由输出可知,192.168.1.220主机处于UP状态,并且主机开放了22端口,同时还侦测到端口对应的服务,最后还给出了目标主机网卡的MAC地址。
了解目标主机的更多信息。
[root@node01 ~]# nmap -T4 -A -v 192.168.1.220`` ``Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-21 13:12 CST``NSE: Loaded 110 scripts for scanning.``NSE: Script Pre-scanning.``Initiating ARP Ping Scan at 13:12``Scanning 192.168.1.220 [1 port]``Completed ARP Ping Scan at 13:12, 0.00s elapsed (1 total hosts)``Initiating Parallel DNS resolution of 1 host. at 13:12``Completed Parallel DNS resolution of 1 host. at 13:12, 0.01s elapsed``Initiating SYN Stealth Scan at 13:12``Scanning 192.168.1.220 [1000 ports]``Discovered open port 22/tcp on 192.168.1.220``Completed SYN Stealth Scan at 13:12, 0.05s elapsed (1000 total ports)``Initiating Service scan at 13:12``Scanning 1 service on 192.168.1.220``Completed Service scan at 13:12, 0.04s elapsed (1 service on 1 host)``Initiating OS detection (try #1) against 192.168.1.220``Retrying OS detection (try #2) against 192.168.1.220``Retrying OS detection (try #3) against 192.168.1.220``Retrying OS detection (try #4) against 192.168.1.220``Retrying OS detection (try #5) against 192.168.1.220``NSE: Script scanning 192.168.1.220.``Initiating NSE at 13:13``Completed NSE at 13:13, 0.08s elapsed``Nmap scan report for 192.168.1.220``Host is up (0.00089s latency).``Not shown: 999 closed ports``PORT STATE SERVICE VERSION``22/tcp open ssh OpenSSH 7.4 (protocol 2.0)``| ssh-hostkey: 2048 e5:a6:1b:ba:13:4e:84:7e:21:2e:4f:23:f6:0e:a8:80 (RSA)``|_256 6c:e7:fe:f6:b4:a6:b1:e4:04:47:fc:6b:e6:51:55:8b (ECDSA)``MAC Address: 00:0C:29:C5:19:99 (VMware)``No exact OS matches for host (If you know what OS is running on it, see http://nmap.org/submit/ ).``TCP/IP fingerprint:``OS:SCAN(V=6.40%E=4%D=3/21%OT=22%CT=1%CU=33000%PV=Y%DS=1%DC=D%G=Y%M=000C29%T``OS:M=5E75A260%P=x86_64-redhat-linux-gnu)SEQ(SP=106%GCD=1%ISR=10E%TI=Z%TS=A)``OS:OPS(O1=M5B4ST11NW7%O2=M5B4ST11NW7%O3=M5B4NNT11NW7%O4=M5B4ST11NW7%O5=M5B4``OS:ST11NW7%O6=M5B4ST11)WIN(W1=7120%W2=7120%W3=7120%W4=7120%W5=7120%W6=7120)``OS:ECN(R=Y%DF=Y%T=40%W=7210%O=M5B4NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%``OS:F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T``OS:5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=``OS:Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF``OS:=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40``OS:%CD=S)`` ``Uptime guess: 0.004 days (since Sat Mar 21 13:07:06 2020)``Network Distance: 1 hop``TCP Sequence Prediction: Difficulty=262 (Good luck!)``IP ID Sequence Generation: All zeros`` ``TRACEROUTE``HOP RTT ADDRESS``1 0.89 ms 192.168.1.220`` ``NSE: Script Post-scanning.``Initiating NSE at 13:13``Completed NSE at 13:13, 0.00s elapsed``Read data files from: /usr/bin/../share/nmap``OS and Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .``Nmap done: 1 IP address (1 host up) scanned in 12.57 seconds` `Raw packets sent: 1111 (52.918KB) | Rcvd: 1072 (46.334KB)
-A:用于开启全面扫描,
-T4:指定扫描过程中使用的时序的模板,总共有6个等级(0~5),等级越高扫描速度越快,但也越容易被防火墙或者入侵检测设备发现并屏蔽,推荐使用-T4。
-v:显示扫描细节。
第一部分是对主机是否在线的扫描
Host is up (0.00068s latency).
第二部分是对端口进行扫描,在默认情况下nmap会扫描1000个最有可能会开放的端口,因为只扫描到22号端口是开放的,所以在输出中会显示
Not shown: 999 closed ports
第三部分是对端口上运行的服务以及版本号进行统计
PORT STATE SERVICE VERSION``22/tcp open ssh OpenSSH 7.4 (protocol 2.0)``| ssh-hostkey: 2048 e5:a6:1b:ba:13:4e:84:7e:21:2e:4f:23:f6:0e:a8:80 (RSA)``|_256 6c:e7:fe:f6:b4:a6:b1:e4:04:47:fc:6b:e6:51:55:8b (ECDSA)
第四部分是对操作系统类型和版本进行探测。
No exact OS matches for host (If you know what OS is running on it, see http://nmap.org/submit/ ).
第五部分是对目标主机路由跟踪信息。
TRACEROUTE``HOP RTT ADDRESS``1 0.75 ms 192.168.1.220
nmap主机发现方法
| 选项 | |
| -sn | 只进行主机发现扫描,不进行端口扫描 |
| -Pn | 路过主机发现扫描,将所有指定的主机都视为在线状态,进行端口扫描 |
| -sL | 仅仅列出指定主机的IP地址,不进行主机发现扫描 |
| -PS/PA/PU/PY[printlist] | 指定nmap使用TCP SYN、TCP ACK、UDP、SCTP方式进行主机发现,例如:nmap -PS80,21 |
| -PE/PP/PM | 指定nmap使用ICMP echo、timestamp、netmask请求报文发现主机。 |
| -PO | 使用ip协议包探测目标主机是否在线, |
| -n/-R | 指定是否使用DNS解析,其中-n表示不进行dns解析,-R表示总是进行DNS解析 |
比较常用的是-sn和-Pn,
[root@node01 ~]# nmap -sn -PE -PS22,80 -PU53 www.baidu.com`` ``Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-21 13:47 CST``Nmap scan report for www.baidu.com (39.156.66.14)``Host is up (0.019s latency).``Other addresses for www.baidu.com (not scanned): 39.156.66.18``Nmap done: 1 IP address (1 host up) scanned in 6.59 seconds
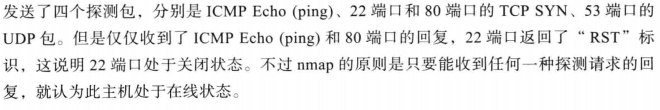
nmap端口扫描
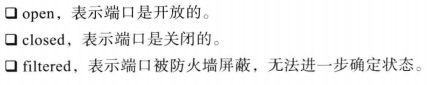
侦测到的端口状态分为6种状态。
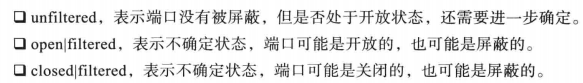
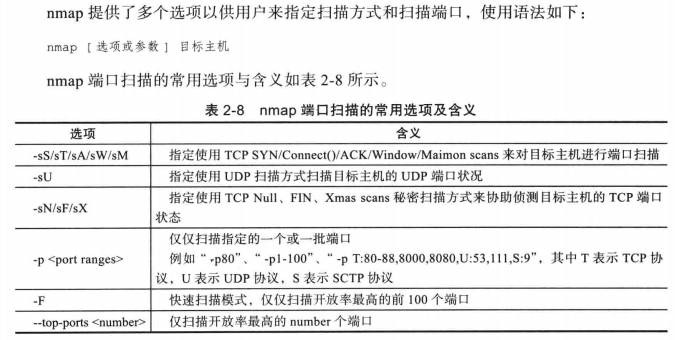
端口扫描的用法
[root@node01 ~]# nmap -sS -sU -F www.baidu.com`` ``Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-21 14:09 CST``Nmap scan report for www.baidu.com (39.156.66.18)``Host is up (0.013s latency).``Other addresses for www.baidu.com (not scanned): 39.156.66.14``Not shown: 100 open|filtered ports, 98 filtered ports``PORT STATE SERVICE``80/tcp open http``443/tcp open https`` ``Nmap done: 1 IP address (1 host up) scanned in 10.13 seconds
\-sS:使用TCP SYN扫描TCP端口
\-sU:扫描UDP端口
\-F:表示使用快速扫描方式,扫描最有可能开放的前100个端口,(TCP、UDP各一百个端口)
nmap版本侦测
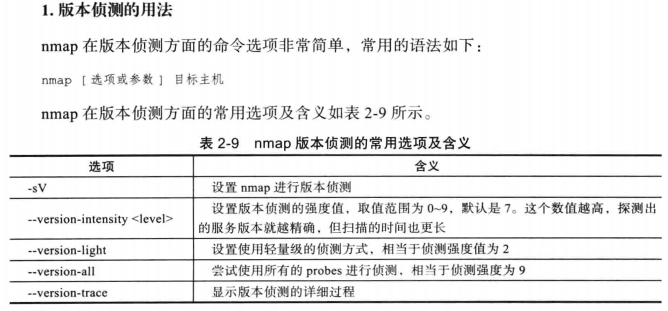
[root@node01 ~]# nmap -sV www.baidu.com`` ``Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-21 14:15 CST``Nmap scan report for www.baidu.com (39.156.66.18)``Host is up (0.016s latency).``Other addresses for www.baidu.com (not scanned): 39.156.66.14``Not shown: 998 filtered ports``PORT STATE SERVICE VERSION``80/tcp open http-proxy sslstrip``443/tcp open ssl/http-proxy sslstrip`` ``Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .``Nmap done: 1 IP address (1 host up) scanned in 27.15 seconds
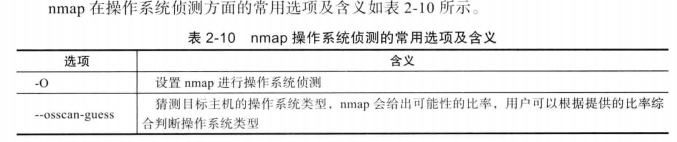
nmap操作系统侦测

黑客/网络安全学习包


资料目录
-
成长路线图&学习规划
-
配套视频教程
-
SRC&黑客文籍
-
护网行动资料
-
黑客必读书单
-
面试题合集
因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取
优快云大礼包:《黑客&网络安全入门&进阶学习资源包》免费分享
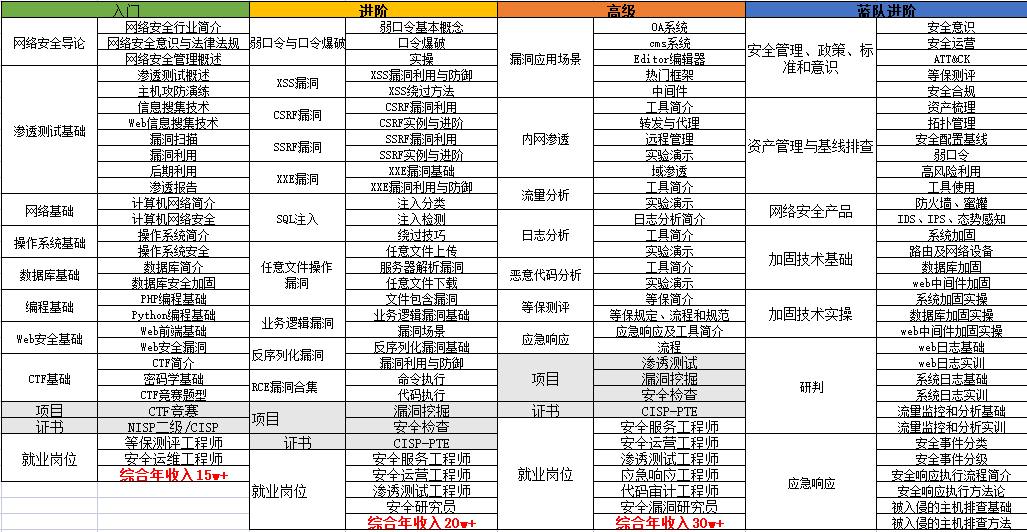
1.成长路线图&学习规划
要学习一门新的技术,作为新手一定要先学习成长路线图,方向不对,努力白费。
对于从来没有接触过网络安全的同学,我们帮你准备了详细的学习成长路线图&学习规划。可以说是最科学最系统的学习路线,大家跟着这个大的方向学习准没问题。

因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取
优快云大礼包:《黑客&网络安全入门&进阶学习资源包》免费分享
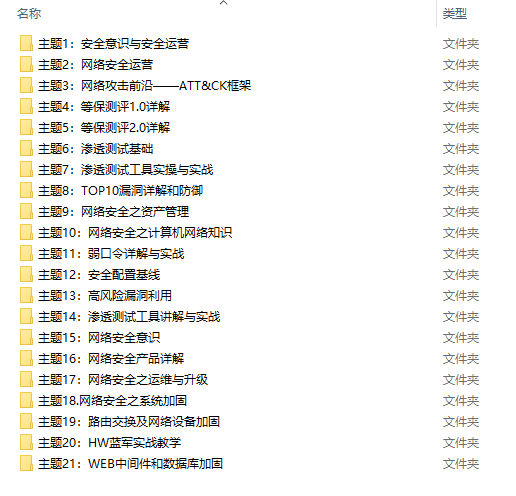
2.视频教程
很多朋友都不喜欢晦涩的文字,我也为大家准备了视频教程,其中一共有21个章节,每个章节都是当前板块的精华浓缩。
因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取
优快云大礼包:《黑客&网络安全入门&进阶学习资源包》免费分享
3.SRC&黑客文籍
大家最喜欢也是最关心的SRC技术文籍&黑客技术也有收录
SRC技术文籍:
黑客资料由于是敏感资源,这里不能直接展示哦!
4.护网行动资料
其中关于HW护网行动,也准备了对应的资料,这些内容可相当于比赛的金手指!
5.黑客必读书单
**

**
6.面试题合集
当你自学到这里,你就要开始思考找工作的事情了,而工作绕不开的就是真题和面试题。
更多内容为防止和谐,可以扫描获取~

因篇幅有限,仅展示部分资料,需要点击下方链接即可前往获取




















 7859
7859

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








